Adzviser
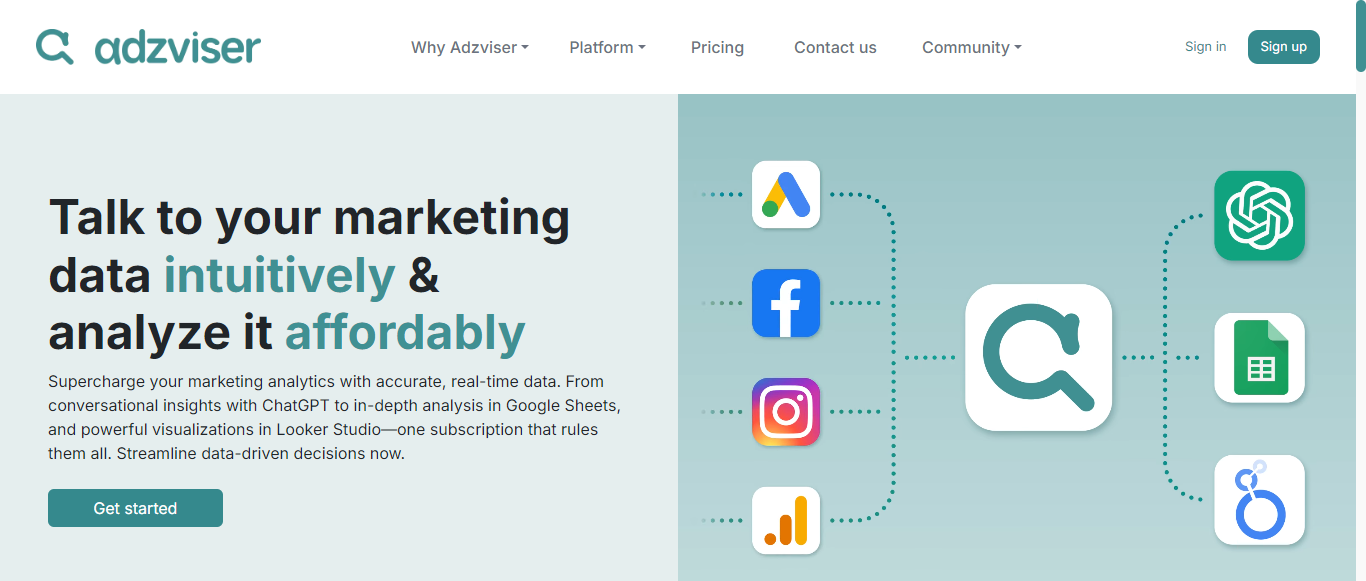
Talk to Your Marketing Data Intuitively

What is Adzviser?
Adzviser is an innovative marketing analytics platform designed to simplify data reporting and analysis for businesses of all sizes. With its intuitive interface, users can engage with their marketing data effortlessly, utilizing tools like ChatGPT for conversational insights, Google Sheets for in-depth analysis, and Looker Studio for powerful visualizations. Adzviser offers flexible connectors to popular data sources such as Google Ads and Facebook Ads, ensuring seamless integration without the need for extensive training. The platform is affordably priced, with a focus on delivering high-quality analytics solutions that cater to startups, in-house teams, and agencies alike. Users benefit from unlimited accounts and queries, customizable dashboards, and exceptional customer support, all while enjoying the peace of mind that comes from a product made and hosted in the USA. Adzviser empowers marketers to make data-driven decisions quickly and efficiently, streamlining their analytics processes and enhancing overall performance.
Adzviser Pricing
Starting from:
$24.99
/month
Adzviser ToS AI Analysis
Last Updated: February 10th, 2025 Tos Average Score: 8.4User Responsibilities and Restrictions:8.5
Intellectual Property Rights:9
Limitation of Liability and Disclaimers:8
Governing Law and Dispute Resolution:8.5
Termination and Account Suspension:8
Summary
Overall, Adzviser's Terms of Service are well-structured and comprehensive, covering essential aspects such as user responsibilities, intellectual property rights, and dispute resolution. While the document is generally user-friendly, there are opportunities for simplification and clarification in certain areas to enhance user comprehension and engagement.
User Responsibilities and Restrictions
8.5
Adzviser clearly outlines user responsibilities and prohibited activities, emphasizing the importance of accurate registration information and the consequences of violations. The extensive list of prohibited actions helps set clear expectations for user behavior, although it could benefit from a more concise summary of key points.
User Responsibilities and Restrictions
8.5
Adzviser clearly outlines user responsibilities and prohibited activities, emphasizing the importance of accurate registration information and the consequences of violations. The extensive list of prohibited actions helps set clear expectations for user behavior, although it could benefit from a more concise summary of key points.
Intellectual Property Rights
9
The section on intellectual property rights is well-articulated, clearly stating that all content and trademarks are owned or licensed by Adzviser. It effectively communicates the limited license granted to users for personal use, while also protecting the company's rights. The emphasis on user-generated content ownership is a positive aspect.
Intellectual Property Rights
9
The section on intellectual property rights is well-articulated, clearly stating that all content and trademarks are owned or licensed by Adzviser. It effectively communicates the limited license granted to users for personal use, while also protecting the company's rights. The emphasis on user-generated content ownership is a positive aspect.
Limitation of Liability and Disclaimers
8
Adzviser includes comprehensive disclaimers regarding the site's availability and the accuracy of its content. The limitations of liability are clearly stated, which is beneficial for the company. However, the language could be simplified for better user understanding, particularly for non-legal audiences.
Limitation of Liability and Disclaimers
8
Adzviser includes comprehensive disclaimers regarding the site's availability and the accuracy of its content. The limitations of liability are clearly stated, which is beneficial for the company. However, the language could be simplified for better user understanding, particularly for non-legal audiences.
Governing Law and Dispute Resolution
8.5
The governing law and dispute resolution section is clear, specifying Delaware law and outlining the arbitration process. The inclusion of informal negotiations before arbitration is a positive aspect, promoting amicable resolutions. However, the complexity of the arbitration process may be daunting for some users.
Governing Law and Dispute Resolution
8.5
The governing law and dispute resolution section is clear, specifying Delaware law and outlining the arbitration process. The inclusion of informal negotiations before arbitration is a positive aspect, promoting amicable resolutions. However, the complexity of the arbitration process may be daunting for some users.
Termination and Account Suspension
8
Adzviser provides a clear framework for account termination and suspension, allowing for user accountability. The terms are straightforward, but the lack of detailed procedures for users to contest a suspension could be improved to enhance transparency and fairness.
Termination and Account Suspension
8
Adzviser provides a clear framework for account termination and suspension, allowing for user accountability. The terms are straightforward, but the lack of detailed procedures for users to contest a suspension could be improved to enhance transparency and fairness.
Adzviser Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8.7Data Collection:8.5
Data Usage:9
Data Sharing and Disclosure:8
User Rights and Controls:9.5
Data Security and Retention:8.5
Summary
Overall, Adzviser's Privacy Policy is well-structured and informative, providing clear insights into data collection, usage, and user rights. The strengths lie in its transparency regarding user rights and data usage, while areas for improvement include more detailed descriptions of data sharing practices and security measures. The policy effectively balances user privacy with operational needs.
Data Collection
8.5
Adzviser provides a clear overview of the types of personal information collected, including names, email addresses, and payment data. The policy specifies that sensitive personal information is not processed and that no information is received from third parties. However, it could benefit from more detail on the automatic data collection methods and the specific types of cookies used.
Data Collection
8.5
Adzviser provides a clear overview of the types of personal information collected, including names, email addresses, and payment data. The policy specifies that sensitive personal information is not processed and that no information is received from third parties. However, it could benefit from more detail on the automatic data collection methods and the specific types of cookies used.
Data Usage
9
The policy effectively outlines the various purposes for which user data is processed, including service improvement, communication, and legal compliance. It also mentions marketing communications and user support, providing a transparent view of data usage. However, a more explicit mention of analytics and personalization could enhance clarity.
Data Usage
9
The policy effectively outlines the various purposes for which user data is processed, including service improvement, communication, and legal compliance. It also mentions marketing communications and user support, providing a transparent view of data usage. However, a more explicit mention of analytics and personalization could enhance clarity.
Data Sharing and Disclosure
8
Adzviser clearly states the circumstances under which personal information may be shared, including business transfers and third-party partnerships. The policy references adherence to Google API Services User Data Policy, which is a positive aspect. However, it could improve by detailing the specific third-party partners and the types of data shared with them.
Data Sharing and Disclosure
8
Adzviser clearly states the circumstances under which personal information may be shared, including business transfers and third-party partnerships. The policy references adherence to Google API Services User Data Policy, which is a positive aspect. However, it could improve by detailing the specific third-party partners and the types of data shared with them.
User Rights and Controls
9.5
The policy provides comprehensive information on user rights, including access, deletion, and opting out of marketing communications. It outlines actionable steps for users to exercise these rights, which is commendable. The inclusion of specific rights for California and Virginia residents adds to its thoroughness.
User Rights and Controls
9.5
The policy provides comprehensive information on user rights, including access, deletion, and opting out of marketing communications. It outlines actionable steps for users to exercise these rights, which is commendable. The inclusion of specific rights for California and Virginia residents adds to its thoroughness.
Data Security and Retention
8.5
Adzviser describes the security measures in place to protect personal information and outlines the retention policy, stating that data will be kept only as long as necessary. While the security measures are generally well-articulated, the policy could benefit from more specific examples of the technical safeguards employed.
Data Security and Retention
8.5
Adzviser describes the security measures in place to protect personal information and outlines the retention policy, stating that data will be kept only as long as necessary. While the security measures are generally well-articulated, the policy could benefit from more specific examples of the technical safeguards employed.
Adzviser Rating
Not rated yet
0 ratings