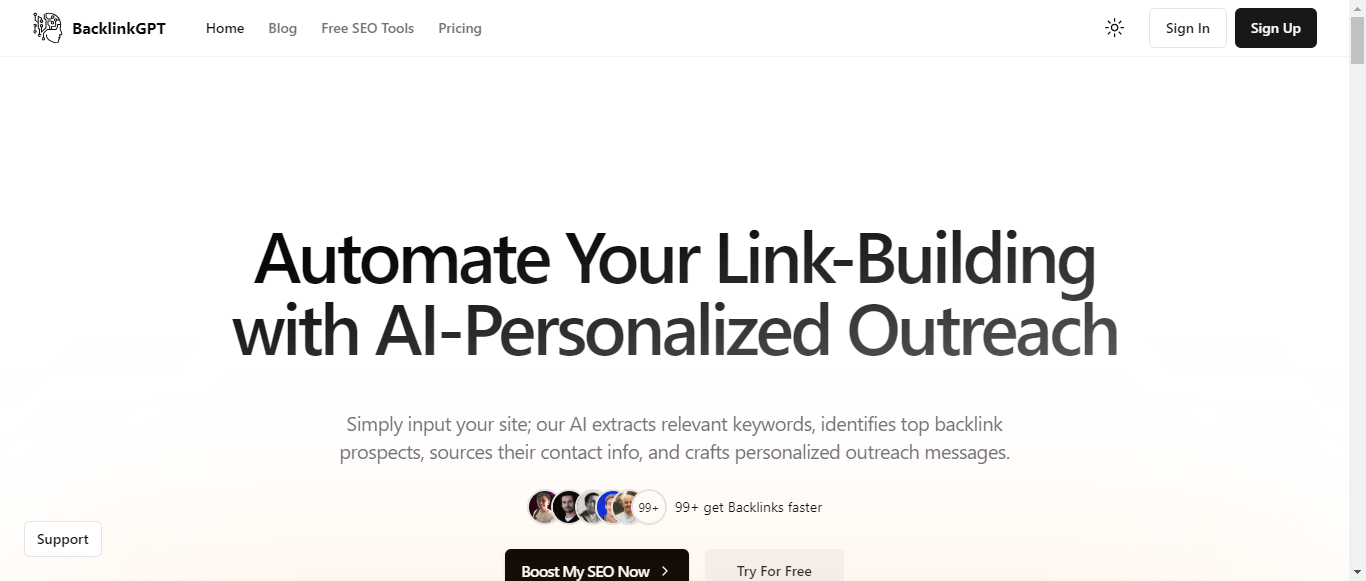
BacklinkGPT
Automate Your Link-Building with AI-Personalized Outreach
What is BacklinkGPT?
BacklinkGPT is an AI-powered link-building platform designed to streamline the process of acquiring valuable backlinks for websites. By simply inputting your site, users can leverage advanced AI technology to extract relevant keywords, identify top backlink prospects, and automate personalized outreach messages. The platform offers seamless email integration, allowing users to manage their campaigns and track responses directly from the interface. With features like one-click link prospecting and automated contact discovery, BacklinkGPT significantly reduces the time and effort required for effective link-building. Various pricing plans cater to teams of all sizes, making it accessible for small businesses and SEO professionals alike. Trusted by website owners worldwide, BacklinkGPT aims to revolutionize backlink strategies and enhance SEO performance through innovative AI solutions.
Categories
BacklinkGPT Pricing
Starting from:
$49.99
/month
BacklinkGPT ToS AI Analysis
Last Updated: February 10th, 2025 Tos Average Score: 8.4User Responsibilities and Restrictions:8.5
Intellectual Property Rights:9
Limitation of Liability and Disclaimers:8
Governing Law and Dispute Resolution:8.5
Termination and Account Suspension:8
Summary
Overall, BacklinkGPT's Terms of Service are well-structured and cover essential areas effectively. The sections on user responsibilities and intellectual property rights stand out for their clarity and comprehensiveness. While the limitation of liability and dispute resolution sections are solid, simplifying the language and providing more user-friendly explanations could enhance user understanding. The termination policy is clear but could benefit from more transparency regarding the appeal process. The overall master score reflects a strong foundation with room for improvement in user accessibility.
User Responsibilities and Restrictions
8.5
BacklinkGPT outlines clear user responsibilities, emphasizing the need for accurate information and lawful use of the service. It effectively prohibits various harmful activities, such as impersonation and unauthorized access, which helps maintain a safe environment. However, the section could benefit from more explicit examples of prohibited behaviors to enhance user understanding.
User Responsibilities and Restrictions
8.5
BacklinkGPT outlines clear user responsibilities, emphasizing the need for accurate information and lawful use of the service. It effectively prohibits various harmful activities, such as impersonation and unauthorized access, which helps maintain a safe environment. However, the section could benefit from more explicit examples of prohibited behaviors to enhance user understanding.
Intellectual Property Rights
9
The intellectual property rights section is comprehensive, clearly stating that all rights to the service's materials are owned by BacklinkGPT or its licensors. It also provides users with limited rights to use the materials, which is well-articulated. The mention of third-party content sources, like Moz and Microsoft, adds transparency, though it could further clarify user rights regarding their own content.
Intellectual Property Rights
9
The intellectual property rights section is comprehensive, clearly stating that all rights to the service's materials are owned by BacklinkGPT or its licensors. It also provides users with limited rights to use the materials, which is well-articulated. The mention of third-party content sources, like Moz and Microsoft, adds transparency, though it could further clarify user rights regarding their own content.
Limitation of Liability and Disclaimers
8
BacklinkGPT includes a robust limitation of liability clause, effectively protecting itself from various claims. The disclaimers regarding the service's reliability and accuracy are clear, which is important for user awareness. However, the language could be simplified to enhance user comprehension, as some legal jargon may be difficult for the average user to understand.
Limitation of Liability and Disclaimers
8
BacklinkGPT includes a robust limitation of liability clause, effectively protecting itself from various claims. The disclaimers regarding the service's reliability and accuracy are clear, which is important for user awareness. However, the language could be simplified to enhance user comprehension, as some legal jargon may be difficult for the average user to understand.
Governing Law and Dispute Resolution
8.5
The governing law and dispute resolution section specifies that German law applies and outlines the arbitration process, which is beneficial for clarity. The mention of waiving the right to a jury trial is a standard practice, but it may be perceived as unfavorable by users. Providing more information on the arbitration process could improve user confidence in the resolution mechanism.
Governing Law and Dispute Resolution
8.5
The governing law and dispute resolution section specifies that German law applies and outlines the arbitration process, which is beneficial for clarity. The mention of waiving the right to a jury trial is a standard practice, but it may be perceived as unfavorable by users. Providing more information on the arbitration process could improve user confidence in the resolution mechanism.
Termination and Account Suspension
8
BacklinkGPT provides a clear framework for account termination and suspension, allowing users to terminate their accounts at any time. The company's right to suspend accounts for violations is also well-stated. However, the process for users to appeal or understand the reasons for suspension could be more transparent, enhancing fairness.
Termination and Account Suspension
8
BacklinkGPT provides a clear framework for account termination and suspension, allowing users to terminate their accounts at any time. The company's right to suspend accounts for violations is also well-stated. However, the process for users to appeal or understand the reasons for suspension could be more transparent, enhancing fairness.
BacklinkGPT Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8.2Data Collection:8.5
Data Usage:8
Data Sharing and Disclosure:7.5
User Rights and Controls:9
Data Security and Retention:8
Summary
Overall, BacklinkGPT's Privacy Policy is well-structured and informative, providing clear insights into data collection, usage, and user rights. While it excels in user rights and controls, there are opportunities for improvement in detailing data sharing practices and providing specific examples in data usage. The policy demonstrates a commitment to user privacy and security.
Data Collection
8.5
BacklinkGPT provides a comprehensive overview of the types of data collected, including Personally Identifiable Information and Non-Personally Identifiable Information. The methods of collection are clearly stated, such as through user interactions and analytics tracking. However, the policy could benefit from more explicit examples of the types of non-personally identifiable information collected.
Data Collection
8.5
BacklinkGPT provides a comprehensive overview of the types of data collected, including Personally Identifiable Information and Non-Personally Identifiable Information. The methods of collection are clearly stated, such as through user interactions and analytics tracking. However, the policy could benefit from more explicit examples of the types of non-personally identifiable information collected.
Data Usage
8
The policy outlines various purposes for data usage, including service operation, communication, and legal compliance. It is transparent about the use of data for analytics and improving services. However, it could enhance clarity by providing more specific examples of how data is used for marketing and personalization.
Data Usage
8
The policy outlines various purposes for data usage, including service operation, communication, and legal compliance. It is transparent about the use of data for analytics and improving services. However, it could enhance clarity by providing more specific examples of how data is used for marketing and personalization.
Data Sharing and Disclosure
7.5
BacklinkGPT clearly states that personal data may be shared with group companies and third-party service providers for specific purposes. It emphasizes that data will not be sold and outlines conditions for legal disclosures. However, the policy could improve by detailing the types of third parties involved and the specific circumstances under which data may be shared.
Data Sharing and Disclosure
7.5
BacklinkGPT clearly states that personal data may be shared with group companies and third-party service providers for specific purposes. It emphasizes that data will not be sold and outlines conditions for legal disclosures. However, the policy could improve by detailing the types of third parties involved and the specific circumstances under which data may be shared.
User Rights and Controls
9
The policy effectively outlines user rights under data protection laws, including access, rectification, and deletion. It provides actionable steps for users to exercise these rights, which is commendable. The inclusion of rights specific to California residents is a strong point, enhancing user empowerment.
User Rights and Controls
9
The policy effectively outlines user rights under data protection laws, including access, rectification, and deletion. It provides actionable steps for users to exercise these rights, which is commendable. The inclusion of rights specific to California residents is a strong point, enhancing user empowerment.
Data Security and Retention
8
BacklinkGPT describes various security measures in place to protect personal information, including encryption and restricted access. The retention policy is clear, stating that data will be kept until a deletion request is made. However, it could provide more detail on the specific security technologies used.
Data Security and Retention
8
BacklinkGPT describes various security measures in place to protect personal information, including encryption and restricted access. The retention policy is clear, stating that data will be kept until a deletion request is made. However, it could provide more detail on the specific security technologies used.
BacklinkGPT Rating
Not rated yet
0 ratings