Bash
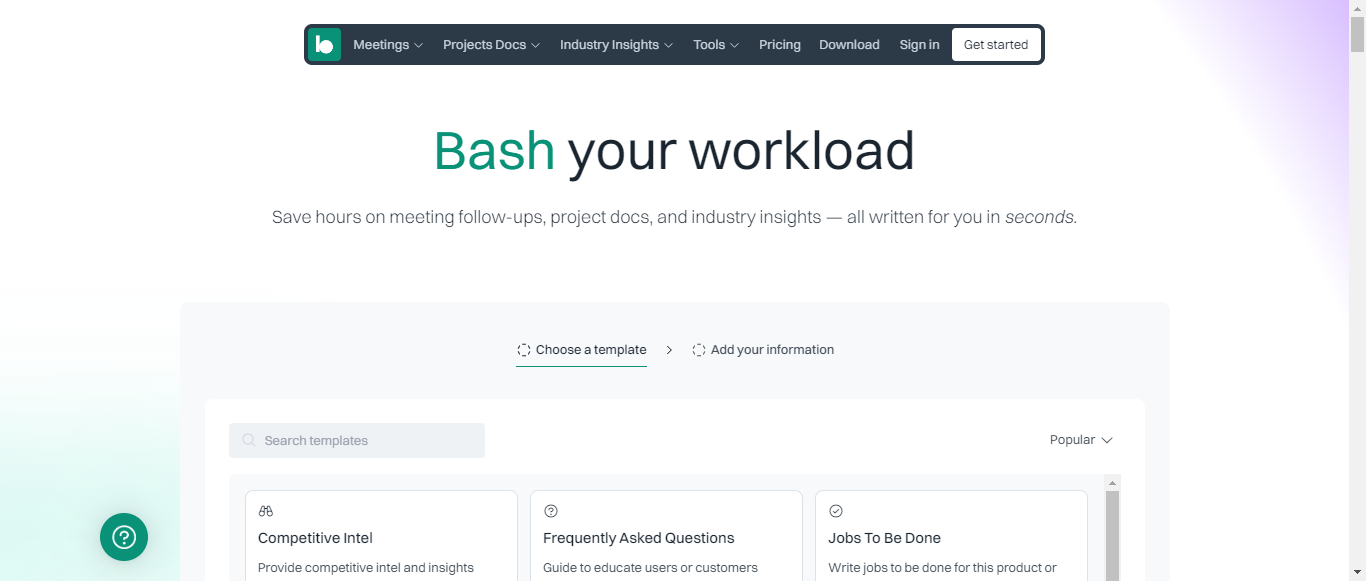
Bash Your Workload: Streamline Meetings, Docs, and Insights Effortlessly!

What is Bash?
Bash is an innovative productivity tool designed to streamline meeting management, project documentation, and competitive intelligence. With over 75 smart templates and AI-driven features, Bash enables users to efficiently record meetings, summarize key points, and create actionable plans in seconds. The platform consolidates various sources of information, allowing teams to stay organized and informed about industry trends and competitor activities. Users can easily generate documents such as PRDs, user stories, and marketing materials, all while ensuring collaboration and customization. Bash's freemium model offers 100 free credits monthly, making it accessible for teams looking to enhance their productivity without upfront costs. With secure cloud storage and GDPR compliance, Bash prioritizes user data safety while providing a comprehensive solution for modern work environments.
Categories
Content Marketing Digital Marketing Marketing Automation Sales Enablement Marketing Competitive Intelligence Business Intelligence Marketing Analytics Video Marketing Product Marketing Business Process Automation Business Process Management Business Strategy Sales Automation Business Communication Productivity Tools Content Creation Meeting Management
Bash Pricing
Freemium
Starting from:
$9.99
/month
Bash ToS AI Analysis
Last Updated: February 10th, 2025 Tos Average Score: 8.4User Responsibilities and Restrictions:8.5
Intellectual Property Rights:9
Limitation of Liability and Disclaimers:8
Governing Law and Dispute Resolution:8.5
Termination and Account Suspension:8
Summary
Overall, Bash's Terms of Service are well-structured and cover essential aspects of user responsibilities, intellectual property, liability, dispute resolution, and account management. While the document is generally clear and comprehensive, there are opportunities for improvement in simplifying language and enhancing user understanding in certain areas. The average score reflects a solid foundation with room for refinement.
User Responsibilities and Restrictions
8.5
Bash outlines clear user responsibilities and restrictions, emphasizing the importance of lawful and ethical use of the Services. The section effectively details prohibited activities, such as sharing accounts and engaging in harmful behaviors. However, it could benefit from more explicit examples of acceptable use to enhance user understanding.
User Responsibilities and Restrictions
8.5
Bash outlines clear user responsibilities and restrictions, emphasizing the importance of lawful and ethical use of the Services. The section effectively details prohibited activities, such as sharing accounts and engaging in harmful behaviors. However, it could benefit from more explicit examples of acceptable use to enhance user understanding.
Intellectual Property Rights
9
The Terms provide a comprehensive overview of intellectual property rights, clearly stating that Bash owns the Services and the content therein. It also addresses user-generated content, granting Bash a broad license to use such submissions. This section is well-articulated, but it could further clarify the implications of the license granted by users.
Intellectual Property Rights
9
The Terms provide a comprehensive overview of intellectual property rights, clearly stating that Bash owns the Services and the content therein. It also addresses user-generated content, granting Bash a broad license to use such submissions. This section is well-articulated, but it could further clarify the implications of the license granted by users.
Limitation of Liability and Disclaimers
8
Bash includes a robust limitation of liability clause, effectively minimizing its exposure to various types of damages. The disclaimers regarding the Services being provided 'as-is' are clear. However, the language could be simplified to enhance user comprehension, particularly for those unfamiliar with legal jargon.
Limitation of Liability and Disclaimers
8
Bash includes a robust limitation of liability clause, effectively minimizing its exposure to various types of damages. The disclaimers regarding the Services being provided 'as-is' are clear. However, the language could be simplified to enhance user comprehension, particularly for those unfamiliar with legal jargon.
Governing Law and Dispute Resolution
8.5
The Terms specify that California law governs the agreement and outline a clear arbitration process for dispute resolution. The inclusion of an opt-out option for arbitration is a positive aspect. However, the complexity of the arbitration process may deter some users, and a more straightforward explanation could improve accessibility.
Governing Law and Dispute Resolution
8.5
The Terms specify that California law governs the agreement and outline a clear arbitration process for dispute resolution. The inclusion of an opt-out option for arbitration is a positive aspect. However, the complexity of the arbitration process may deter some users, and a more straightforward explanation could improve accessibility.
Termination and Account Suspension
8
Bash provides clear conditions under which accounts may be terminated or suspended, emphasizing user responsibility. The potential consequences of termination are well-articulated. However, the process for users to appeal or understand the reasons for termination could be more transparent.
Termination and Account Suspension
8
Bash provides clear conditions under which accounts may be terminated or suspended, emphasizing user responsibility. The potential consequences of termination are well-articulated. However, the process for users to appeal or understand the reasons for termination could be more transparent.
Bash Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8.6Data Collection:8.5
Data Usage:9
Data Sharing and Disclosure:8
User Rights and Controls:9
Data Security and Retention:8.5
Summary
Overall, Bash's Privacy Policy is well-structured and informative, providing clear insights into data collection, usage, sharing, user rights, and security measures. The policy excels in transparency and user empowerment, though there is room for improvement in detailing third-party data sharing and specific security practices. The overall master score reflects a strong commitment to user privacy.
Data Collection
8.5
Bash provides a comprehensive overview of the types of personal data collected, including categories such as identifying information, commercial data, geolocation data, and more. The methods of collection are clearly stated, including direct user input and automatic data collection through cookies. However, a more detailed explanation of the specific types of data collected from third-party sources could enhance transparency.
Data Collection
8.5
Bash provides a comprehensive overview of the types of personal data collected, including categories such as identifying information, commercial data, geolocation data, and more. The methods of collection are clearly stated, including direct user input and automatic data collection through cookies. However, a more detailed explanation of the specific types of data collected from third-party sources could enhance transparency.
Data Usage
9
The policy outlines a variety of purposes for data usage, including service improvement, marketing, and legal compliance. Bash is transparent about how data is used for analytics and personalization, which is commendable. The clarity in explaining the business purposes for data collection is a strong point.
Data Usage
9
The policy outlines a variety of purposes for data usage, including service improvement, marketing, and legal compliance. Bash is transparent about how data is used for analytics and personalization, which is commendable. The clarity in explaining the business purposes for data collection is a strong point.
Data Sharing and Disclosure
8
Bash clearly describes the circumstances under which personal data may be shared with third parties, including service providers and advertising partners. The policy also mentions potential data sales, which is important for user awareness. However, more detail on the specific types of third parties involved could improve user understanding.
Data Sharing and Disclosure
8
Bash clearly describes the circumstances under which personal data may be shared with third parties, including service providers and advertising partners. The policy also mentions potential data sales, which is important for user awareness. However, more detail on the specific types of third parties involved could improve user understanding.
User Rights and Controls
9
The policy effectively outlines user rights, including access, deletion, and the ability to opt-out of data sales. It provides clear instructions on how users can exercise these rights, which is user-friendly. The inclusion of state-specific rights, such as those for California and Nevada residents, adds to its comprehensiveness.
User Rights and Controls
9
The policy effectively outlines user rights, including access, deletion, and the ability to opt-out of data sales. It provides clear instructions on how users can exercise these rights, which is user-friendly. The inclusion of state-specific rights, such as those for California and Nevada residents, adds to its comprehensiveness.
Data Security and Retention
8.5
Bash describes various security measures in place to protect personal data and outlines retention policies, indicating that data is kept as long as necessary for service provision. However, more specific details on the security measures employed could enhance user confidence in data protection.
Data Security and Retention
8.5
Bash describes various security measures in place to protect personal data and outlines retention policies, indicating that data is kept as long as necessary for service provision. However, more specific details on the security measures employed could enhance user confidence in data protection.
Bash Rating
Not rated yet
0 ratings
Bash Comments
total: 0Bash AI Tool Family