BizPlanner AI
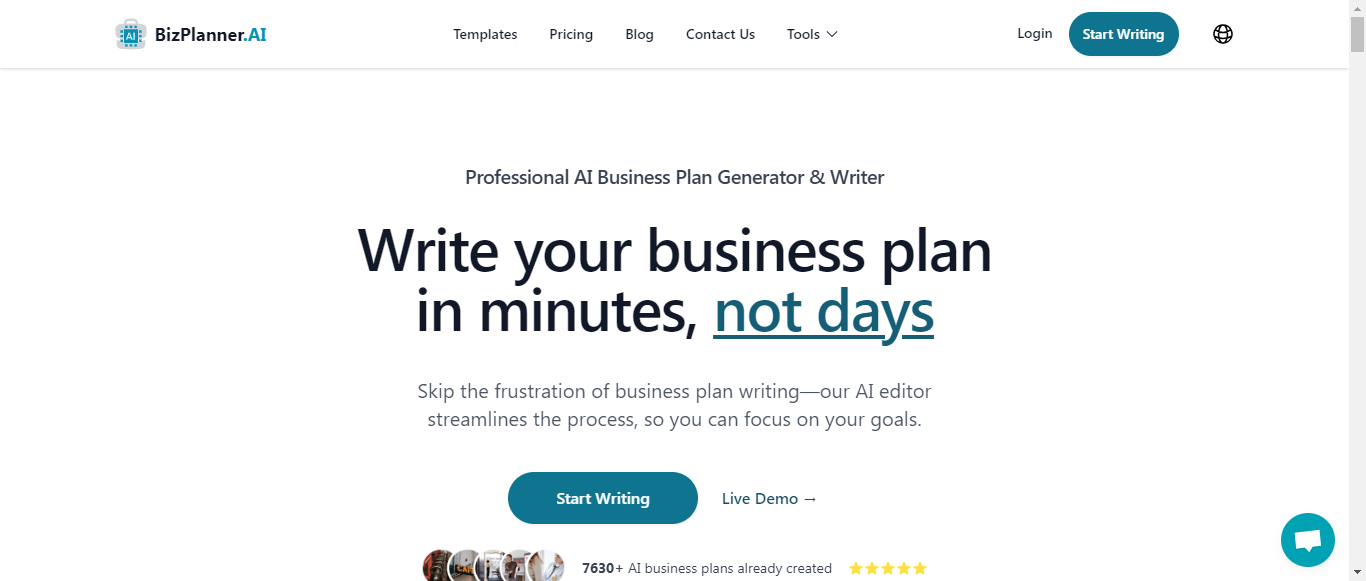
Craft Your Business Plan in 15 Minutes with AI Precision

What is BizPlanner AI?
BizPlanner AI is a professional business plan generator that allows entrepreneurs to create customized business plans in under 15 minutes. Utilizing advanced AI technology, the platform simplifies the often daunting task of business plan writing, enabling users to focus on their business goals. With over 4,630 successful plans generated, BizPlanner offers a user-friendly interface for editing and formatting, along with the ability to export plans in PDF or Word formats. The service includes comprehensive sections covering everything from executive summaries to financial projections, ensuring a thorough overview of business strategies. Priced affordably at $8.99 per plan, BizPlanner AI is designed to save time and money, making quality business planning accessible to all. With positive testimonials from satisfied users worldwide, BizPlanner AI stands out as a valuable tool for entrepreneurs looking to streamline their planning process.
Categories
BizPlanner AI Pricing
Starting from:
$9.99
/month
BizPlanner AI ToS AI Analysis
Last Updated: February 10th, 2025 Tos Average Score: 8.4User Responsibilities and Restrictions:8.5
Intellectual Property Rights:8
Limitation of Liability and Disclaimers:9
Governing Law and Dispute Resolution:8.5
Termination and Account Suspension:8
Summary
Overall, BizPlanner AI's Terms of Service are well-structured and provide clear guidelines for users. The sections on user responsibilities and limitations of liability are particularly strong, while the intellectual property rights and termination processes could benefit from additional clarity. The service effectively balances user rights with the company's protections, making it a solid framework for user engagement.
User Responsibilities and Restrictions
8.5
BizPlanner AI clearly outlines user responsibilities, including maintaining account security and providing accurate information. The prohibited conduct section is comprehensive, detailing unacceptable behaviors, which helps set clear expectations for users.
User Responsibilities and Restrictions
8.5
BizPlanner AI clearly outlines user responsibilities, including maintaining account security and providing accurate information. The prohibited conduct section is comprehensive, detailing unacceptable behaviors, which helps set clear expectations for users.
Intellectual Property Rights
8
The section on intellectual property rights effectively establishes ownership of the service and user-generated content. Users retain rights to their content but grant BizPlanner AI a broad license, which is standard practice. However, the distinction regarding content generated by OpenAI could be clearer.
Intellectual Property Rights
8
The section on intellectual property rights effectively establishes ownership of the service and user-generated content. Users retain rights to their content but grant BizPlanner AI a broad license, which is standard practice. However, the distinction regarding content generated by OpenAI could be clearer.
Limitation of Liability and Disclaimers
9
BizPlanner AI provides a robust disclaimer regarding the service's 'as-is' nature and limits liability effectively. The clarity in outlining potential damages and the scope of liability is commendable, ensuring users understand the risks involved.
Limitation of Liability and Disclaimers
9
BizPlanner AI provides a robust disclaimer regarding the service's 'as-is' nature and limits liability effectively. The clarity in outlining potential damages and the scope of liability is commendable, ensuring users understand the risks involved.
Governing Law and Dispute Resolution
8.5
The governing law is clearly stated as the Netherlands, and the dispute resolution process includes informal resolution steps and arbitration. This structure is user-friendly, although more detail on the arbitration process could enhance understanding.
Governing Law and Dispute Resolution
8.5
The governing law is clearly stated as the Netherlands, and the dispute resolution process includes informal resolution steps and arbitration. This structure is user-friendly, although more detail on the arbitration process could enhance understanding.
Termination and Account Suspension
8
The conditions for account termination and suspension are well-defined, allowing users to understand the potential consequences of their actions. However, the lack of a detailed appeal process for users could be seen as a drawback.
Termination and Account Suspension
8
The conditions for account termination and suspension are well-defined, allowing users to understand the potential consequences of their actions. However, the lack of a detailed appeal process for users could be seen as a drawback.
BizPlanner AI Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8.4Data Collection:8.5
Data Usage:9
Data Sharing and Disclosure:8
User Rights and Controls:8.5
Data Security and Retention:8
Summary
Overall, BizPlanner AI's Privacy Policy is well-structured and informative, providing clear insights into data collection, usage, sharing, user rights, and security measures. While it excels in transparency and user empowerment, there are areas for improvement, particularly in detailing third-party data collection methods and security protocols. The policy effectively balances user privacy with operational needs, making it a strong framework for protecting user information.
Data Collection
8.5
BizPlanner AI provides a comprehensive overview of the types of data collected, including personal information, business plan data, usage information, and device details. The methods of collection are clearly stated, such as through account registration and cookies. However, more detail on how data is collected from third-party services could enhance transparency.
Data Collection
8.5
BizPlanner AI provides a comprehensive overview of the types of data collected, including personal information, business plan data, usage information, and device details. The methods of collection are clearly stated, such as through account registration and cookies. However, more detail on how data is collected from third-party services could enhance transparency.
Data Usage
9
The policy clearly outlines the purposes for which data is used, including service enhancement, communication, security, analytics, and marketing. It emphasizes user consent for marketing communications, which is a positive aspect. The transparency regarding the use of data for analytics and improvement is commendable.
Data Usage
9
The policy clearly outlines the purposes for which data is used, including service enhancement, communication, security, analytics, and marketing. It emphasizes user consent for marketing communications, which is a positive aspect. The transparency regarding the use of data for analytics and improvement is commendable.
Data Sharing and Disclosure
8
BizPlanner AI provides a clear explanation of data sharing with third-party service providers, detailing their roles and the necessity of sharing. However, the policy could benefit from more explicit examples of circumstances under which data might be shared with law enforcement or in legal situations.
Data Sharing and Disclosure
8
BizPlanner AI provides a clear explanation of data sharing with third-party service providers, detailing their roles and the necessity of sharing. However, the policy could benefit from more explicit examples of circumstances under which data might be shared with law enforcement or in legal situations.
User Rights and Controls
8.5
The policy effectively outlines user rights, including access, correction, deletion, and objection to processing. It provides actionable steps for users to exercise these rights, which is a strong point. However, the process for verifying identity before fulfilling requests could be elaborated for clarity.
User Rights and Controls
8.5
The policy effectively outlines user rights, including access, correction, deletion, and objection to processing. It provides actionable steps for users to exercise these rights, which is a strong point. However, the process for verifying identity before fulfilling requests could be elaborated for clarity.
Data Security and Retention
8
BizPlanner AI describes various security measures in place to protect personal information, such as encryption and secure storage. The data retention policy is well-defined, explaining how long data is kept and the criteria for retention. However, more detail on the specific security protocols and regular audits could enhance user confidence.
Data Security and Retention
8
BizPlanner AI describes various security measures in place to protect personal information, such as encryption and secure storage. The data retention policy is well-defined, explaining how long data is kept and the criteria for retention. However, more detail on the specific security protocols and regular audits could enhance user confidence.
BizPlanner AI Rating
Not rated yet
0 ratings
BizPlanner AI Comments
total: 0BizPlanner AI AI Tool Family