
Chat Data
Empower Your Data with Custom AI Chatbots 24/7
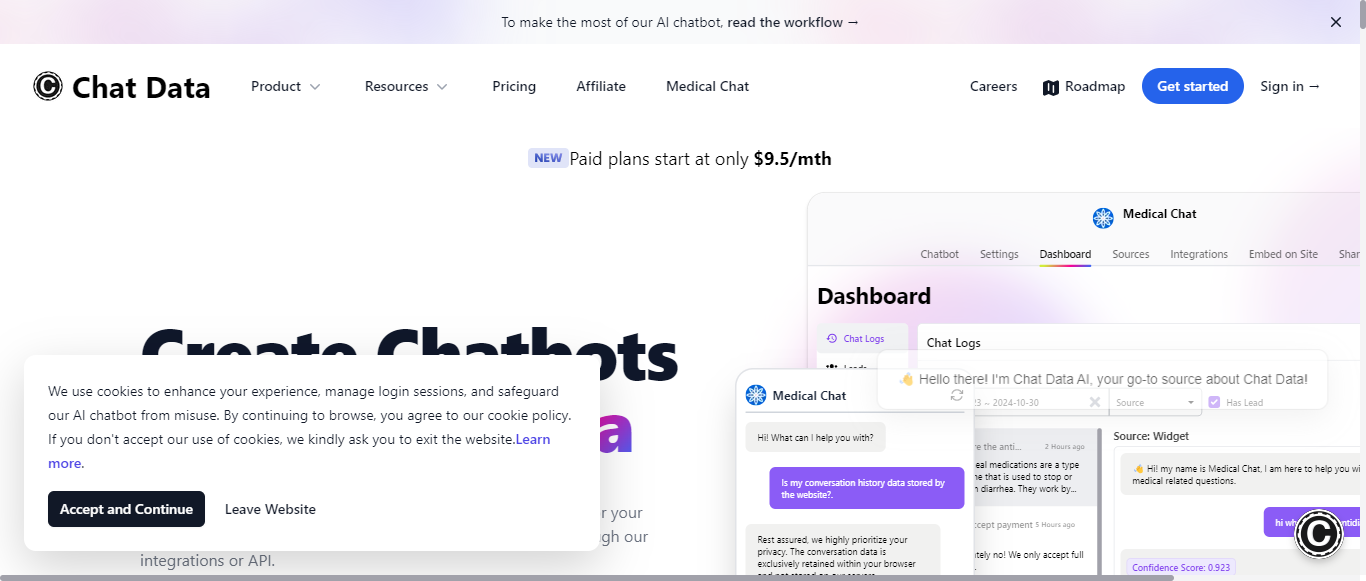

What is Chat Data?
Chat Data offers a versatile AI chatbot service that integrates seamlessly with your data sources, allowing you to create customized chatbots for your website. With plans starting at just $9.50 per month, users can build chatbots that reflect their brand's personality and engage customers effectively. The platform supports real-time voice interactions, multi-modal inputs, and dynamic query suggestions, enhancing user experience. Privacy is a priority, with conversation data retained only within the user's browser. Chat Data also provides advanced features like live chat escalation, third-party integrations, and the ability to create medical chatbots compliant with HIPAA standards. Users can personalize their chatbots with various training data formats and easily embed them on their sites. The service is designed for flexibility and collaboration, making it suitable for businesses looking to enhance customer engagement and streamline support.
Categories
Chat Data Pricing
Freemium
Starting from:
$7.5
/month
Chat Data ToS AI Analysis
Last Updated: February 10th, 2025 Tos Average Score: 8.2User Responsibilities and Restrictions:8.5
Intellectual Property Rights:9
Limitation of Liability and Disclaimers:8
Governing Law and Dispute Resolution:7.5
Termination and Account Suspension:8
Summary
Overall, the Terms of Service for Chat Data are well-structured and provide clear guidelines for users. The sections on user responsibilities and intellectual property rights are particularly strong, while the limitation of liability and governing law sections could benefit from clearer language and more detailed dispute resolution procedures. The Terms effectively balance user rights and company protections, fostering a transparent relationship.
User Responsibilities and Restrictions
8.5
Chat Data outlines clear user responsibilities and restrictions, emphasizing lawful use and prohibiting harmful activities. The section effectively details prohibited behaviors, such as impersonation and the use of automated means to access the service, which helps maintain a safe environment for all users.
User Responsibilities and Restrictions
8.5
Chat Data outlines clear user responsibilities and restrictions, emphasizing lawful use and prohibiting harmful activities. The section effectively details prohibited behaviors, such as impersonation and the use of automated means to access the service, which helps maintain a safe environment for all users.
Intellectual Property Rights
9
The Terms provide a comprehensive overview of intellectual property rights, clearly stating that the Company retains ownership of its content while allowing users to maintain rights to their own submissions. The licensing terms are well-defined, ensuring users understand their rights and limitations regarding their content.
Intellectual Property Rights
9
The Terms provide a comprehensive overview of intellectual property rights, clearly stating that the Company retains ownership of its content while allowing users to maintain rights to their own submissions. The licensing terms are well-defined, ensuring users understand their rights and limitations regarding their content.
Limitation of Liability and Disclaimers
8
Chat Data includes robust disclaimers regarding the service's reliability and accuracy, which is essential for managing user expectations. However, the language could be simplified for better clarity, as some users may find legal jargon challenging to understand.
Limitation of Liability and Disclaimers
8
Chat Data includes robust disclaimers regarding the service's reliability and accuracy, which is essential for managing user expectations. However, the language could be simplified for better clarity, as some users may find legal jargon challenging to understand.
Governing Law and Dispute Resolution
7.5
The governing law is specified as the State of California, which is standard practice. However, the Terms could benefit from more detailed procedures for dispute resolution, such as mediation or arbitration, to provide users with a clearer understanding of their options.
Governing Law and Dispute Resolution
7.5
The governing law is specified as the State of California, which is standard practice. However, the Terms could benefit from more detailed procedures for dispute resolution, such as mediation or arbitration, to provide users with a clearer understanding of their options.
Termination and Account Suspension
8
The conditions for account termination and suspension are clearly stated, allowing users to understand the potential consequences of their actions. However, the process could be enhanced by including more information on how users can appeal or seek clarification regarding account actions.
Termination and Account Suspension
8
The conditions for account termination and suspension are clearly stated, allowing users to understand the potential consequences of their actions. However, the process could be enhanced by including more information on how users can appeal or seek clarification regarding account actions.
Chat Data Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8Data Collection:8.5
Data Usage:8
Data Sharing and Disclosure:7.5
User Rights and Controls:8
Data Security and Retention:8
Summary
Overall, Chat Data's Privacy Policy is well-structured and provides a clear understanding of data collection, usage, and user rights. It effectively communicates its commitment to data security and user privacy. Areas for improvement include providing more specific examples of data types collected, enhancing transparency around marketing data usage, and detailing scenarios for data sharing with law enforcement.
Data Collection
8.5
Chat Data provides a comprehensive overview of the types of data collected, including personal information, usage data, and cookies. The methods of collection are clearly stated, detailing both user-provided information and automatic collection through cookies. However, it could benefit from more specific examples of the types of personal information collected.
Data Collection
8.5
Chat Data provides a comprehensive overview of the types of data collected, including personal information, usage data, and cookies. The methods of collection are clearly stated, detailing both user-provided information and automatic collection through cookies. However, it could benefit from more specific examples of the types of personal information collected.
Data Usage
8
The policy outlines various purposes for data usage, including service provision, communication, and analytics. It is transparent about the use of analytics tools like Google Analytics and Mixpanel. However, further clarification on how marketing data is used could enhance transparency.
Data Usage
8
The policy outlines various purposes for data usage, including service provision, communication, and analytics. It is transparent about the use of analytics tools like Google Analytics and Mixpanel. However, further clarification on how marketing data is used could enhance transparency.
Data Sharing and Disclosure
7.5
Chat Data mentions the use of third-party service providers and the conditions under which data may be shared. While it emphasizes that third parties are bound by contractual obligations, it could improve by detailing specific scenarios where data might be shared with law enforcement or other entities.
Data Sharing and Disclosure
7.5
Chat Data mentions the use of third-party service providers and the conditions under which data may be shared. While it emphasizes that third parties are bound by contractual obligations, it could improve by detailing specific scenarios where data might be shared with law enforcement or other entities.
User Rights and Controls
8
The policy effectively outlines user rights, including access, correction, and deletion of personal information. It provides clear contact information for users to exercise these rights, which is commendable. However, it could include more detailed instructions on the process for opting out of marketing communications.
User Rights and Controls
8
The policy effectively outlines user rights, including access, correction, and deletion of personal information. It provides clear contact information for users to exercise these rights, which is commendable. However, it could include more detailed instructions on the process for opting out of marketing communications.
Data Security and Retention
8
Chat Data describes the security measures in place to protect personal information and outlines data retention practices. The mention of organizational and technical processes is reassuring, but the policy could benefit from more specific details on the duration of data retention and the security technologies employed.
Data Security and Retention
8
Chat Data describes the security measures in place to protect personal information and outlines data retention practices. The mention of organizational and technical processes is reassuring, but the policy could benefit from more specific details on the duration of data retention and the security technologies employed.
Chat Data Rating
Not rated yet
0 ratings