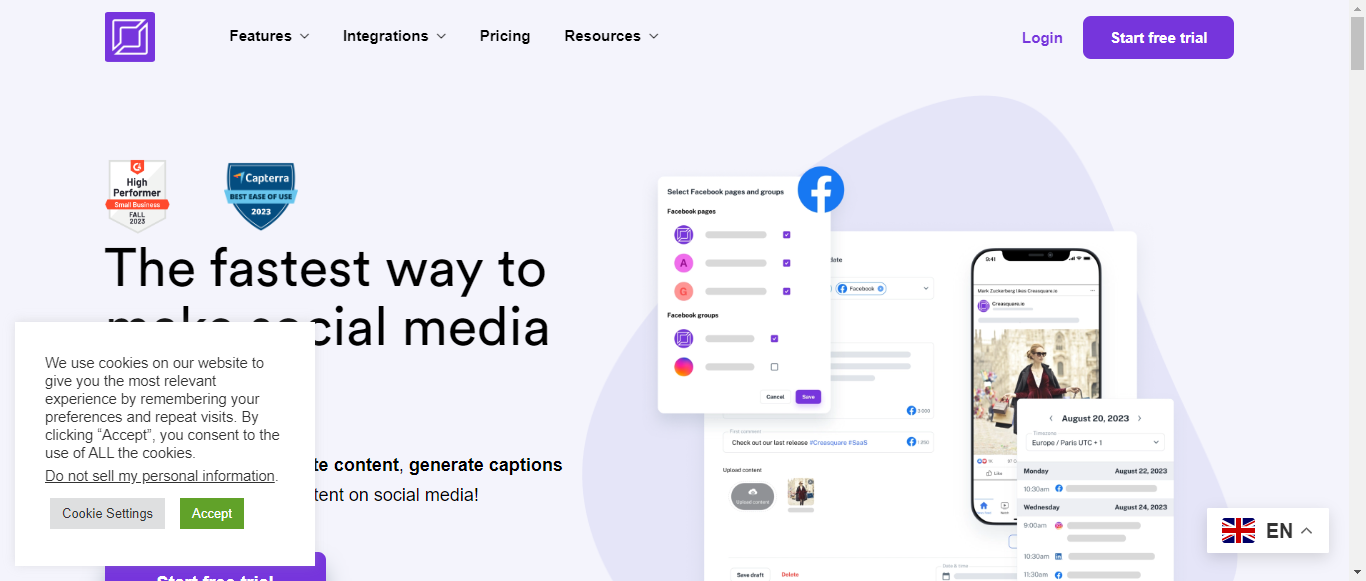
Creasquare
Create, Schedule, and Shine: Your All-in-One Digital Content Solution

What is Creasquare?
Creasquare is an innovative AI-powered digital content solution designed to streamline the creation, scheduling, and management of social media content. With features like an AI Content Writer, Creative Studio, and a comprehensive content calendar, users can effortlessly generate engaging graphics, videos, and captions tailored to their brand's voice. The platform supports integration with major social media channels such as Facebook, Instagram, YouTube, LinkedIn, and TikTok, allowing for seamless content distribution. Creasquare aims to save time and enhance productivity by enabling users to schedule posts in batches and visualize their content strategy. With over 10,000 businesses already benefiting from its tools, Creasquare is positioned as a go-to resource for marketers looking to optimize their digital presence. Users can start with a free trial, making it easy to explore the platform's capabilities without commitment.
Categories
Creasquare Pricing
Free Trial
Starting from:
$24.9
/month
Creasquare ToS AI Analysis
Last Updated: February 10th, 2025 Tos Average Score: 8.2User Responsibilities and Restrictions:8.5
Intellectual Property Rights:9
Limitation of Liability and Disclaimers:8
Governing Law and Dispute Resolution:7.5
Termination and Account Suspension:8
Summary
Overall, Creasquare's Terms of Service are well-structured and cover essential aspects of user responsibilities, intellectual property, and liability. While the document is generally clear, there are opportunities for improvement in simplifying legal language and enhancing user recourse options in dispute resolution.
User Responsibilities and Restrictions
8.5
Creasquare outlines clear user responsibilities, including prohibitions against modifying, copying, or distributing content without permission. The section effectively emphasizes compliance with laws and third-party terms, which is crucial for maintaining a respectful and lawful user environment.
User Responsibilities and Restrictions
8.5
Creasquare outlines clear user responsibilities, including prohibitions against modifying, copying, or distributing content without permission. The section effectively emphasizes compliance with laws and third-party terms, which is crucial for maintaining a respectful and lawful user environment.
Intellectual Property Rights
9
The terms provide a comprehensive overview of intellectual property rights, clearly stating that users retain ownership of their content while granting Creasquare a license to use it. This balance protects user rights while allowing the platform to operate effectively.
Intellectual Property Rights
9
The terms provide a comprehensive overview of intellectual property rights, clearly stating that users retain ownership of their content while granting Creasquare a license to use it. This balance protects user rights while allowing the platform to operate effectively.
Limitation of Liability and Disclaimers
8
Creasquare includes robust disclaimers regarding the service's availability and performance, limiting liability for indirect damages. However, the language could be simplified for better user understanding, particularly for those less familiar with legal jargon.
Limitation of Liability and Disclaimers
8
Creasquare includes robust disclaimers regarding the service's availability and performance, limiting liability for indirect damages. However, the language could be simplified for better user understanding, particularly for those less familiar with legal jargon.
Governing Law and Dispute Resolution
7.5
The governing law is clearly stated as that of France, with a specific jurisdiction for disputes. While this is beneficial for clarity, the absence of alternative dispute resolution options may limit user recourse in certain situations.
Governing Law and Dispute Resolution
7.5
The governing law is clearly stated as that of France, with a specific jurisdiction for disputes. While this is beneficial for clarity, the absence of alternative dispute resolution options may limit user recourse in certain situations.
Termination and Account Suspension
8
The terms provide a clear framework for account termination and suspension, allowing for immediate action in case of breaches. However, more detail on the appeal process or user notification prior to termination could enhance transparency.
Termination and Account Suspension
8
The terms provide a clear framework for account termination and suspension, allowing for immediate action in case of breaches. However, more detail on the appeal process or user notification prior to termination could enhance transparency.
Creasquare Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8.6Data Collection:8.5
Data Usage:9
Data Sharing and Disclosure:8
User Rights and Controls:9
Data Security and Retention:8.5
Summary
Overall, Creasquare's Privacy Policy is well-structured and informative, providing a solid understanding of data collection, usage, sharing, user rights, and security measures. The policy excels in transparency and user rights but could benefit from additional details in certain areas to enhance clarity and user-friendliness.
Data Collection
8.5
Creasquare provides a comprehensive overview of the types of personal information collected, including voluntarily provided data (e.g., name, email, payment details) and automatically collected data (e.g., device information, log data). The policy clearly outlines the methods of collection, but could benefit from more specific examples of how data is collected in practice.
Data Collection
8.5
Creasquare provides a comprehensive overview of the types of personal information collected, including voluntarily provided data (e.g., name, email, payment details) and automatically collected data (e.g., device information, log data). The policy clearly outlines the methods of collection, but could benefit from more specific examples of how data is collected in practice.
Data Usage
9
The policy effectively details the various purposes for which personal data is used, including service provision, customization, communication, analytics, and marketing. It emphasizes transparency and legal compliance, which is commendable. However, a clearer distinction between different types of data usage could enhance understanding.
Data Usage
9
The policy effectively details the various purposes for which personal data is used, including service provision, customization, communication, analytics, and marketing. It emphasizes transparency and legal compliance, which is commendable. However, a clearer distinction between different types of data usage could enhance understanding.
Data Sharing and Disclosure
8
Creasquare outlines the circumstances under which personal information may be shared with third parties, including service providers and legal authorities. The policy lists specific third-party services used, which adds transparency. However, it could improve by providing more detail on the criteria for sharing data and the safeguards in place.
Data Sharing and Disclosure
8
Creasquare outlines the circumstances under which personal information may be shared with third parties, including service providers and legal authorities. The policy lists specific third-party services used, which adds transparency. However, it could improve by providing more detail on the criteria for sharing data and the safeguards in place.
User Rights and Controls
9
The policy thoroughly explains user rights regarding personal information, including access, rectification, erasure, and objection to processing. It provides clear instructions on how users can exercise these rights, which is a strong point. However, a more user-friendly format or summary of rights could enhance accessibility.
User Rights and Controls
9
The policy thoroughly explains user rights regarding personal information, including access, rectification, erasure, and objection to processing. It provides clear instructions on how users can exercise these rights, which is a strong point. However, a more user-friendly format or summary of rights could enhance accessibility.
Data Security and Retention
8.5
Creasquare describes the security measures in place to protect personal information and outlines the retention policy, stating that data will only be kept as long as necessary. While the information is generally clear, more specifics on the security protocols and retention timelines would strengthen this section.
Data Security and Retention
8.5
Creasquare describes the security measures in place to protect personal information and outlines the retention policy, stating that data will only be kept as long as necessary. While the information is generally clear, more specifics on the security protocols and retention timelines would strengthen this section.
Creasquare Rating
Not rated yet
0 ratings
Creasquare Comments
total: 0Creasquare AI Tool Family