Credal
Empower Your Team to Build Secure AI Solutions with Confidence
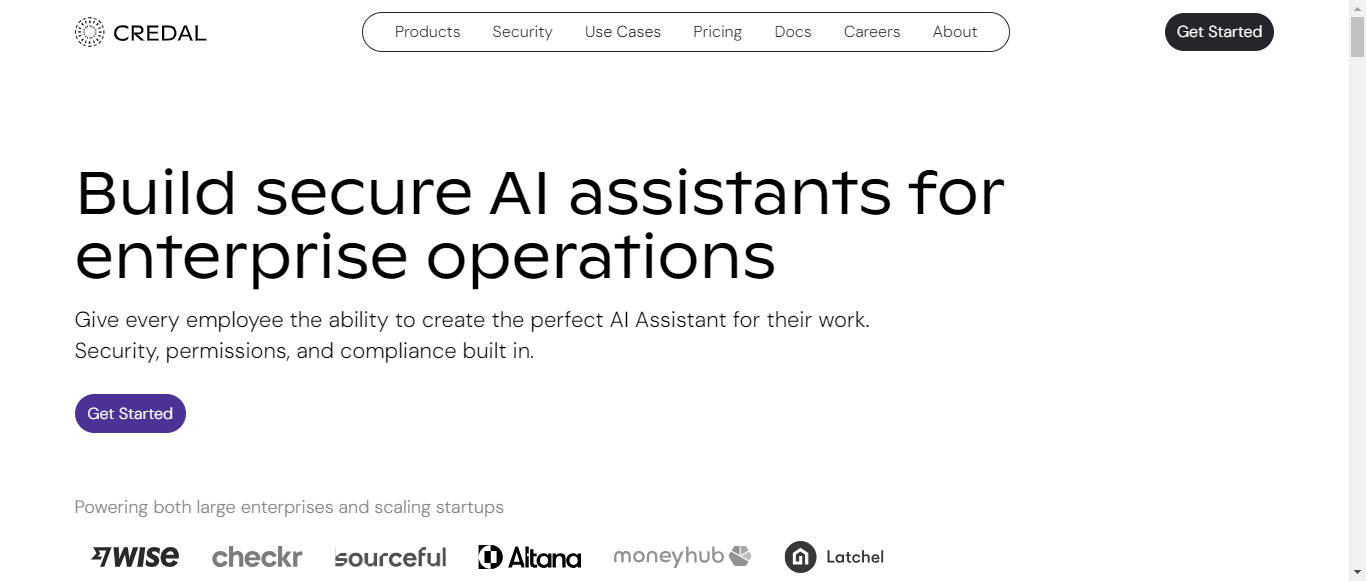
What is Credal?
Credal is a robust platform designed to empower enterprises and startups to build secure AI applications using their own data. With a focus on security, compliance, and user-friendly integration, Credal allows employees to create customized AI assistants tailored to their specific operational needs. The platform supports seamless data integration from various sources, ensuring that permissions and access controls are inherited and enforced. It features a flexible API for developers, enabling the creation of AI-powered applications with ease. Credal prioritizes data protection by offering automatic redaction of personally identifiable information (PII) and comprehensive audit capabilities to maintain compliance with regulations like HIPAA. With point-and-click integrations and support for both cloud and on-premise deployments, Credal is positioned as a leading solution for enterprises looking to leverage generative AI securely and efficiently.
Categories
Credal Pricing
-- No pricing available --
Credal ToS AI Analysis
Last Updated: February 10th, 2025 Tos Average Score: 6.8User Responsibilities and Restrictions:6
Intellectual Property Rights:7.5
Limitation of Liability and Disclaimers:8
Governing Law and Dispute Resolution:5.5
Termination and Account Suspension:7
Summary
Overall, the Terms of Service for Credal provide a foundational understanding of user responsibilities, intellectual property, and liability limitations. However, there are areas for improvement, particularly in clarifying user restrictions, dispute resolution processes, and the treatment of user-generated content. Enhancing these sections could lead to a more user-friendly experience.
User Responsibilities and Restrictions
6
The Terms of Service outline user responsibilities and restrictions, but specific prohibited activities or behaviors are not clearly defined. This could lead to ambiguity for users regarding acceptable use.
User Responsibilities and Restrictions
6
The Terms of Service outline user responsibilities and restrictions, but specific prohibited activities or behaviors are not clearly defined. This could lead to ambiguity for users regarding acceptable use.
Intellectual Property Rights
7.5
Credal asserts ownership over its content and services, but the treatment of user-generated content is not explicitly detailed. Clearer guidelines on user rights and licenses would enhance understanding.
Intellectual Property Rights
7.5
Credal asserts ownership over its content and services, but the treatment of user-generated content is not explicitly detailed. Clearer guidelines on user rights and licenses would enhance understanding.
Limitation of Liability and Disclaimers
8
The Terms include limitations on liability and disclaimers regarding service accuracy and availability. However, more specific examples or scenarios could improve clarity for users.
Limitation of Liability and Disclaimers
8
The Terms include limitations on liability and disclaimers regarding service accuracy and availability. However, more specific examples or scenarios could improve clarity for users.
Governing Law and Dispute Resolution
5.5
The governing law and dispute resolution processes are not clearly articulated. Users may benefit from a more detailed explanation of the jurisdiction and procedures for resolving disputes.
Governing Law and Dispute Resolution
5.5
The governing law and dispute resolution processes are not clearly articulated. Users may benefit from a more detailed explanation of the jurisdiction and procedures for resolving disputes.
Termination and Account Suspension
7
The conditions for account termination and suspension are mentioned, but the process lacks transparency. Clearer guidelines on how users can appeal or understand the reasons for suspension would be beneficial.
Termination and Account Suspension
7
The conditions for account termination and suspension are mentioned, but the process lacks transparency. Clearer guidelines on how users can appeal or understand the reasons for suspension would be beneficial.
Credal Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8.2Data Collection:8.5
Data Usage:8
Data Sharing and Disclosure:7.5
User Rights and Controls:9
Data Security and Retention:8
Summary
Overall, Credal's Privacy Policy is well-structured and informative, providing clear insights into data collection, usage, user rights, and security measures. The policy excels in user rights and controls, ensuring users are well-informed about their options. Areas for improvement include providing more specific examples in data collection and sharing practices, as well as enhancing transparency in data usage for analytics and marketing.
Data Collection
8.5
Credal provides a comprehensive overview of the types of personal information collected, including identifiers, commercial information, and sensitive data. The policy clearly outlines the various entities from which data is collected, such as website visitors, customers, end users, and employees. However, it could benefit from more specific examples of the methods used for data collection.
Data Collection
8.5
Credal provides a comprehensive overview of the types of personal information collected, including identifiers, commercial information, and sensitive data. The policy clearly outlines the various entities from which data is collected, such as website visitors, customers, end users, and employees. However, it could benefit from more specific examples of the methods used for data collection.
Data Usage
8
The policy effectively details the purposes for which personal information is used, including service provision, analytics, market research, and legal compliance. It also mentions marketing communications, with an option to opt-out. However, further clarity on how data is used for analytics and marketing could enhance transparency.
Data Usage
8
The policy effectively details the purposes for which personal information is used, including service provision, analytics, market research, and legal compliance. It also mentions marketing communications, with an option to opt-out. However, further clarity on how data is used for analytics and marketing could enhance transparency.
Data Sharing and Disclosure
7.5
Credal outlines the circumstances under which personal information may be shared, including with affiliates, service providers, and for legal obligations. While the policy mentions consent and aggregated data sharing, it could improve by providing more specific examples of third parties involved and the nature of the data shared.
Data Sharing and Disclosure
7.5
Credal outlines the circumstances under which personal information may be shared, including with affiliates, service providers, and for legal obligations. While the policy mentions consent and aggregated data sharing, it could improve by providing more specific examples of third parties involved and the nature of the data shared.
User Rights and Controls
9
The policy provides a thorough explanation of user rights, particularly for California residents and EEA/UK individuals. It details rights related to access, deletion, correction, and portability of data, along with clear instructions on how to exercise these rights. This section is well-structured and user-friendly.
User Rights and Controls
9
The policy provides a thorough explanation of user rights, particularly for California residents and EEA/UK individuals. It details rights related to access, deletion, correction, and portability of data, along with clear instructions on how to exercise these rights. This section is well-structured and user-friendly.
Data Security and Retention
8
Credal describes various security measures in place to protect personal information and outlines data retention practices. The policy states that data is retained only as long as necessary, which is a positive aspect. However, more specific details on the security measures implemented could enhance user confidence.
Data Security and Retention
8
Credal describes various security measures in place to protect personal information and outlines data retention practices. The policy states that data is retained only as long as necessary, which is a positive aspect. However, more specific details on the security measures implemented could enhance user confidence.
Credal Rating
Not rated yet
0 ratings
Credal Comments
total: 0Credal AI Tool Family