
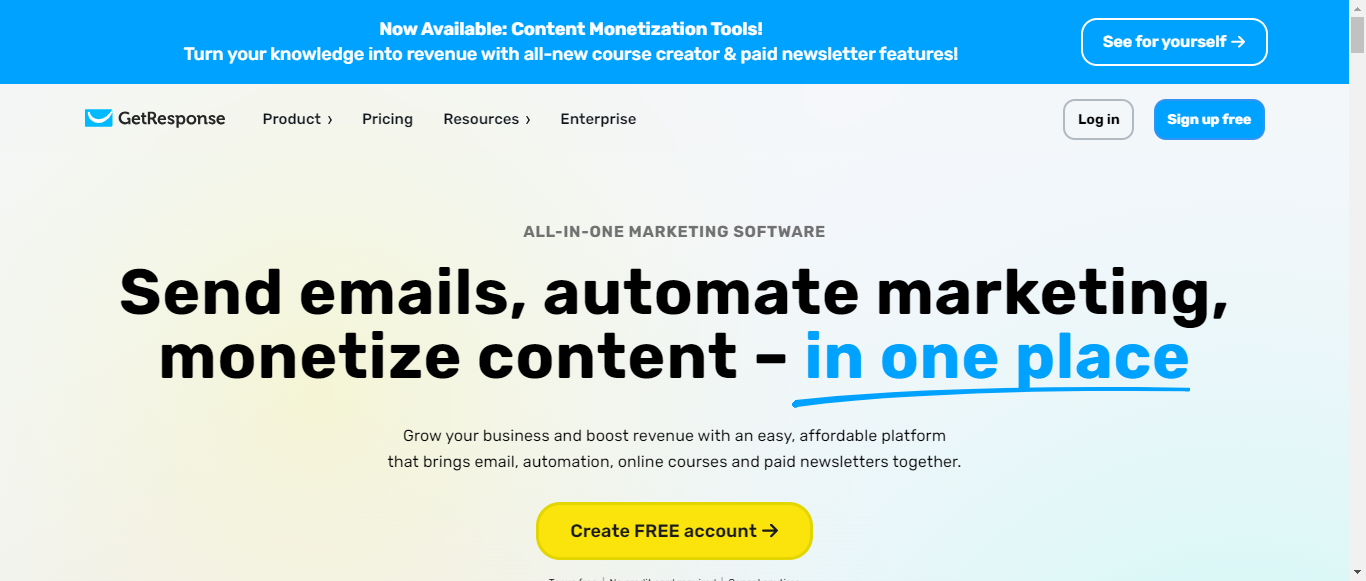
GetResponse
All-in-One Marketing Software to Grow Your Business and Monetize Your Knowledge
What is GetResponse?
GetResponse is an all-in-one marketing software designed for professional email marketing and automation. With features like signup forms, landing pages, and AI-driven tools, it helps businesses grow their email lists and engage subscribers effectively. Users can create and manage email campaigns, automate marketing processes, and promote products through various channels, including SMS and web push notifications. The platform also offers content monetization tools, enabling creators to develop online courses and premium newsletters. GetResponse boasts a 99% deliverability rate and supports over 400,000 customers worldwide, providing 24/7 assistance from a highly-rated customer success team. With affordable pricing plans starting at $19/month, GetResponse integrates seamlessly with over 170 other tools, making it a comprehensive solution for marketers looking to enhance their online presence and maximize revenue.
Categories
GetResponse Pricing
Free Trial
Starting from:
$13
/month
GetResponse Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8.7Data Collection:8.5
Data Usage:9
Data Sharing and Disclosure:8
User Rights and Controls:9.5
Data Security and Retention:8.5
Summary
Overall, GetResponse's Privacy Policy is well-structured and informative, providing clear insights into data collection, usage, user rights, and security measures. The policy excels in transparency regarding user rights and data usage but could benefit from more detailed explanations in certain areas, particularly concerning data sharing and security protocols. The overall score reflects a strong commitment to user privacy and compliance with data protection regulations.
Data Collection
8.5
GetResponse provides a comprehensive overview of the types of personal data collected, including registration data, account details, and data concerning user activity. The methods of collection are clearly stated, such as through registration forms and user interactions with the platform. However, more clarity on the specific types of data collected from third-party sources could enhance transparency.
Data Collection
8.5
GetResponse provides a comprehensive overview of the types of personal data collected, including registration data, account details, and data concerning user activity. The methods of collection are clearly stated, such as through registration forms and user interactions with the platform. However, more clarity on the specific types of data collected from third-party sources could enhance transparency.
Data Usage
9
The policy effectively outlines the various purposes for which GetResponse uses personal data, including service provision, marketing communications, and analytics. It emphasizes transparency regarding the use of data for legitimate interests and marketing, which is commendable. However, a more detailed explanation of how data is used for analytics could further improve user understanding.
Data Usage
9
The policy effectively outlines the various purposes for which GetResponse uses personal data, including service provision, marketing communications, and analytics. It emphasizes transparency regarding the use of data for legitimate interests and marketing, which is commendable. However, a more detailed explanation of how data is used for analytics could further improve user understanding.
Data Sharing and Disclosure
8
GetResponse clearly states that personal data may be shared with service providers and under legal obligations. The policy specifies the types of recipients and the purposes for sharing data, which is beneficial. However, it could provide more detail on the specific circumstances under which data might be shared with law enforcement or other third parties.
Data Sharing and Disclosure
8
GetResponse clearly states that personal data may be shared with service providers and under legal obligations. The policy specifies the types of recipients and the purposes for sharing data, which is beneficial. However, it could provide more detail on the specific circumstances under which data might be shared with law enforcement or other third parties.
User Rights and Controls
9.5
The policy thoroughly explains user rights under GDPR and CCPA, including access, deletion, and the right to withdraw consent. It provides actionable steps for users to exercise these rights, making it user-friendly. The clarity and comprehensiveness of this section are particularly strong.
User Rights and Controls
9.5
The policy thoroughly explains user rights under GDPR and CCPA, including access, deletion, and the right to withdraw consent. It provides actionable steps for users to exercise these rights, making it user-friendly. The clarity and comprehensiveness of this section are particularly strong.
Data Security and Retention
8.5
GetResponse outlines security measures such as encrypted data transmission and specifies data retention periods, including the process for data deletion after account deactivation. While the security measures are adequately described, additional details on specific security protocols could enhance user confidence.
Data Security and Retention
8.5
GetResponse outlines security measures such as encrypted data transmission and specifies data retention periods, including the process for data deletion after account deactivation. While the security measures are adequately described, additional details on specific security protocols could enhance user confidence.
GetResponse Rating
Not rated yet
0 ratings
GetResponse Comments
total: 0GetResponse AI Tool Family