HeadshotPro
Professional Headshots in Minutes with AI Magic
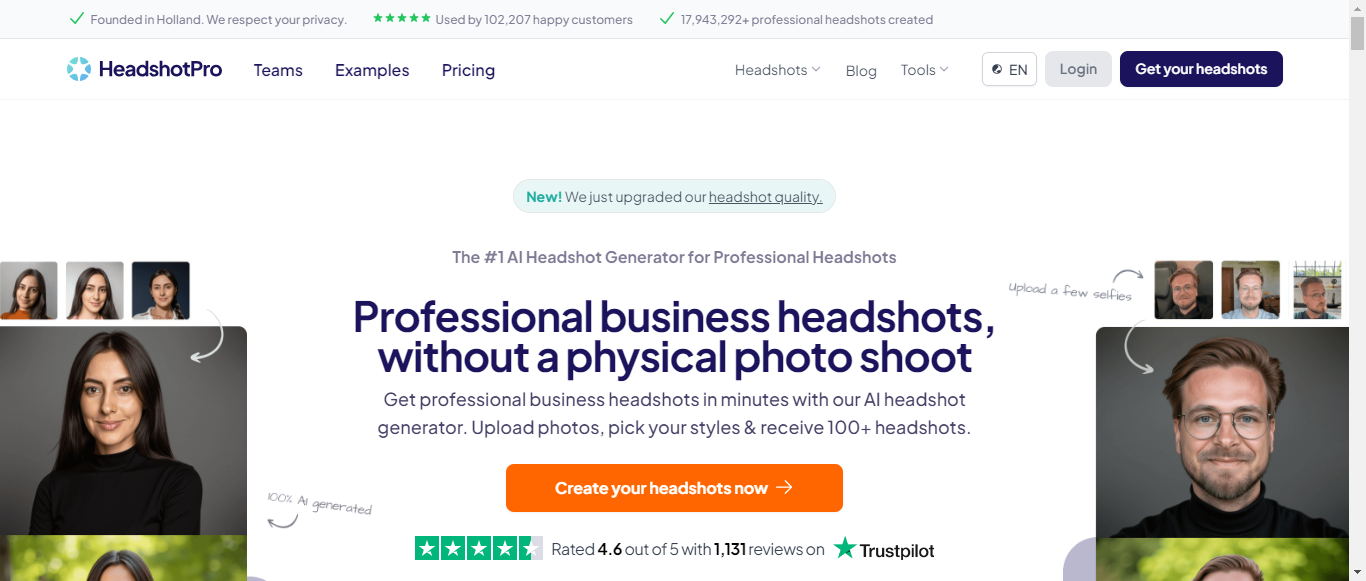

What is HeadshotPro?
HeadshotPro is the leading AI headshot generator, designed to create professional-quality headshots in just minutes. Founded in Holland, the service has garnered over 102,207 satisfied customers and produced more than 17 million headshots. Users can upload their photos, select styles, and receive a diverse range of headshots, all while saving time and money compared to traditional photography. With packages starting at just $29, HeadshotPro offers a cost-effective solution for various needs, including corporate, actor, and LinkedIn headshots. The platform guarantees high-quality results, with a money-back promise if users are not satisfied. Additionally, it provides a suite of free tools for enhancing professional branding, such as email signature and profile picture generators. HeadshotPro prioritizes user privacy, ensuring that uploaded photos are deleted after seven days. Experience the convenience of AI-generated headshots that look indistinguishable from real photos, all from the comfort of your home.
Categories
HeadshotPro Pricing
Starting from:
$29
- 40 headshots
HeadshotPro ToS AI Analysis
Last Updated: February 10th, 2025 Tos Average Score: 8.2User Responsibilities and Restrictions:8.5
Intellectual Property Rights:9
Limitation of Liability and Disclaimers:8
Governing Law and Dispute Resolution:7.5
Termination and Account Suspension:8
Summary
Overall, HeadshotPro's Terms of Service are well-structured and cover essential aspects of user responsibilities, intellectual property, and liability. The clarity in user obligations and ownership rights is commendable. However, improvements could be made in the dispute resolution process and the transparency of account termination procedures to enhance user trust and satisfaction.
User Responsibilities and Restrictions
8.5
HeadshotPro outlines clear user responsibilities and prohibited conduct, including illegal activities, harassment, and unauthorized access. The section effectively communicates the expectations for user behavior, promoting a safe and respectful environment.
User Responsibilities and Restrictions
8.5
HeadshotPro outlines clear user responsibilities and prohibited conduct, including illegal activities, harassment, and unauthorized access. The section effectively communicates the expectations for user behavior, promoting a safe and respectful environment.
Intellectual Property Rights
9
The Terms provide a comprehensive overview of intellectual property rights, clearly stating that users retain ownership of their User Content while granting HeadshotPro a broad license to use it. This balance protects user rights while allowing the company to operate effectively.
Intellectual Property Rights
9
The Terms provide a comprehensive overview of intellectual property rights, clearly stating that users retain ownership of their User Content while granting HeadshotPro a broad license to use it. This balance protects user rights while allowing the company to operate effectively.
Limitation of Liability and Disclaimers
8
HeadshotPro includes extensive disclaimers regarding the service's performance and limitations of liability. While it effectively limits its liability, the language may be perceived as overly protective, which could deter some users from fully trusting the service.
Limitation of Liability and Disclaimers
8
HeadshotPro includes extensive disclaimers regarding the service's performance and limitations of liability. While it effectively limits its liability, the language may be perceived as overly protective, which could deter some users from fully trusting the service.
Governing Law and Dispute Resolution
7.5
The Terms specify that disputes will be resolved through binding arbitration under Singapore law, which may not be favorable for all users. The opt-out option is a positive aspect, but the arbitration process could be more user-friendly and transparent.
Governing Law and Dispute Resolution
7.5
The Terms specify that disputes will be resolved through binding arbitration under Singapore law, which may not be favorable for all users. The opt-out option is a positive aspect, but the arbitration process could be more user-friendly and transparent.
Termination and Account Suspension
8
HeadshotPro provides clear conditions for account termination and suspension, emphasizing user responsibility. However, the lack of a detailed appeal process may leave users feeling uncertain about their rights in case of termination.
Termination and Account Suspension
8
HeadshotPro provides clear conditions for account termination and suspension, emphasizing user responsibility. However, the lack of a detailed appeal process may leave users feeling uncertain about their rights in case of termination.
HeadshotPro Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8.2Data Collection:8.5
Data Usage:8
Data Sharing and Disclosure:7.5
User Rights and Controls:9
Data Security and Retention:8
Summary
Overall, HeadshotPro's Privacy Policy is well-structured and provides a solid foundation for user privacy and data protection. It effectively communicates user rights and data usage, while also outlining security measures. Areas for improvement include providing more detail on data collection methods, third-party sharing practices, and specific security protocols.
Data Collection
8.5
HeadshotPro clearly outlines the types of personal identifiable information collected, including name, email address, and payment information. The policy also mentions the collection of anonymous usage data through optional cookies. However, it could benefit from more detail on the specific methods of data collection and any third-party tools used.
Data Collection
8.5
HeadshotPro clearly outlines the types of personal identifiable information collected, including name, email address, and payment information. The policy also mentions the collection of anonymous usage data through optional cookies. However, it could benefit from more detail on the specific methods of data collection and any third-party tools used.
Data Usage
8
The policy provides a transparent overview of how HeadshotPro uses personal data, including for service access, payment processing, and customer communication. It also mentions the use of anonymous data for service improvement. However, further clarification on marketing practices and how user data may be utilized for analytics could enhance transparency.
Data Usage
8
The policy provides a transparent overview of how HeadshotPro uses personal data, including for service access, payment processing, and customer communication. It also mentions the use of anonymous data for service improvement. However, further clarification on marketing practices and how user data may be utilized for analytics could enhance transparency.
Data Sharing and Disclosure
7.5
HeadshotPro specifies the circumstances under which personal data may be shared, including with partners for essential services and in response to legal requests. While the policy emphasizes that data will be shared only when necessary, it could improve by detailing the types of third parties involved and the safeguards in place for data sharing.
Data Sharing and Disclosure
7.5
HeadshotPro specifies the circumstances under which personal data may be shared, including with partners for essential services and in response to legal requests. While the policy emphasizes that data will be shared only when necessary, it could improve by detailing the types of third parties involved and the safeguards in place for data sharing.
User Rights and Controls
9
The policy effectively outlines user rights under GDPR, including access, rectification, erasure, and objection. It provides clear instructions on how users can exercise these rights, which is commendable. However, it could include more information on the process for data portability.
User Rights and Controls
9
The policy effectively outlines user rights under GDPR, including access, rectification, erasure, and objection. It provides clear instructions on how users can exercise these rights, which is commendable. However, it could include more information on the process for data portability.
Data Security and Retention
8
HeadshotPro describes several security measures in place to protect user data, such as security software and TLS connections. The retention policy is also clearly stated, indicating that data will be deleted upon user request or when no longer necessary. More detail on the specific security protocols and practices could further strengthen this section.
Data Security and Retention
8
HeadshotPro describes several security measures in place to protect user data, such as security software and TLS connections. The retention policy is also clearly stated, indicating that data will be deleted upon user request or when no longer necessary. More detail on the specific security protocols and practices could further strengthen this section.
HeadshotPro Rating
Not rated yet
0 ratings
HeadshotPro Comments
total: 0HeadshotPro AI Tool Family