Monica
Your All-in-One AI Assistant for Effortless Productivity
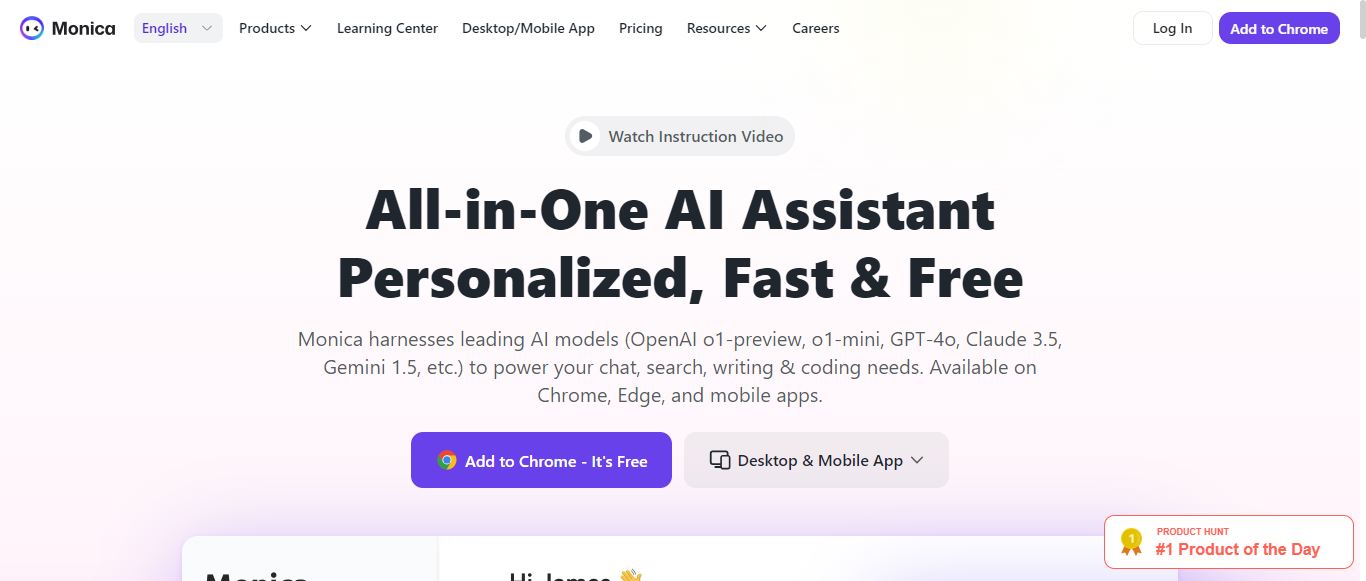
What is Monica?
Monica is an all-in-one AI assistant that integrates advanced models like GPT-4o, Claude 3.5, and Gemini 1.5 to enhance productivity across various tasks. Available as a Chrome extension and mobile app, Monica allows users to chat, write, code, and translate with ease. With features such as instant summarization of web pages and videos, content generation, and real-time web access, Monica saves users significant time and effort. The platform is designed for professionals, offering specialized tools for market intelligence, email management, research assistance, and more. Users can access Monica's capabilities with a simple keyboard shortcut, making it convenient to enhance their workflow. With high ratings on platforms like the Chrome Store and Product Hunt, Monica is praised for its user-friendly interface and powerful functionalities, making it an essential tool for anyone looking to streamline their tasks and unleash their potential.
Categories
Business Process Management Digital Marketing Content Marketing Marketing Video Marketing Business Process Automation Business Management Business Intelligence Business Automation Business Communication Business Development Email marketing Social Media Marketing Marketing Analytics Productivity Marketing Materials Ecommerce Marketing Sales Enablement Recruitment AI Assistant AI Writing AI Translation
Monica Pricing
Has Free Trial or Freemium
Starting from:
$9.9
/month
Monica ToS AI Analysis
Last Updated: February 10th, 2025 Tos Average Score: 8.2User Responsibilities and Restrictions:8.5
Intellectual Property Rights:9
Limitation of Liability and Disclaimers:8
Governing Law and Dispute Resolution:7.5
Termination and Account Suspension:8
Summary
Overall, the Terms of Service for Monica are well-structured and cover essential areas effectively. The sections on user responsibilities and intellectual property rights stand out for their clarity and balance. However, there is room for improvement in simplifying legal language and providing more detailed procedures for dispute resolution and account termination. The overall score reflects a solid foundation with opportunities for enhanced user engagement and understanding.
User Responsibilities and Restrictions
8.5
Monica clearly outlines user responsibilities, including the prohibition of unlawful activities, account sharing, and manipulation of membership status. The section is comprehensive and emphasizes the importance of fair usage, which is commendable. However, it could benefit from more explicit examples of prohibited behaviors to enhance user understanding.
User Responsibilities and Restrictions
8.5
Monica clearly outlines user responsibilities, including the prohibition of unlawful activities, account sharing, and manipulation of membership status. The section is comprehensive and emphasizes the importance of fair usage, which is commendable. However, it could benefit from more explicit examples of prohibited behaviors to enhance user understanding.
Intellectual Property Rights
9
The terms regarding intellectual property rights are well-articulated, specifying that users retain ownership of their content while granting Monica a broad license to use it. This balance is favorable for users. The section could be improved by providing more clarity on how user-generated content may be used by Monica and third parties.
Intellectual Property Rights
9
The terms regarding intellectual property rights are well-articulated, specifying that users retain ownership of their content while granting Monica a broad license to use it. This balance is favorable for users. The section could be improved by providing more clarity on how user-generated content may be used by Monica and third parties.
Limitation of Liability and Disclaimers
8
Monica includes a robust limitation of liability clause, effectively minimizing its exposure to various types of damages. The disclaimers regarding the service's reliability and accuracy are clear, but the language could be simplified for better user comprehension. Overall, it effectively protects the company while informing users of potential risks.
Limitation of Liability and Disclaimers
8
Monica includes a robust limitation of liability clause, effectively minimizing its exposure to various types of damages. The disclaimers regarding the service's reliability and accuracy are clear, but the language could be simplified for better user comprehension. Overall, it effectively protects the company while informing users of potential risks.
Governing Law and Dispute Resolution
7.5
The governing law is clearly stated, and the terms provide a basic framework for dispute resolution. However, the process for resolving disputes could be more detailed, particularly regarding arbitration or mediation procedures. This would enhance transparency and user confidence in the resolution process.
Governing Law and Dispute Resolution
7.5
The governing law is clearly stated, and the terms provide a basic framework for dispute resolution. However, the process for resolving disputes could be more detailed, particularly regarding arbitration or mediation procedures. This would enhance transparency and user confidence in the resolution process.
Termination and Account Suspension
8
Monica outlines the conditions under which accounts may be terminated or suspended, emphasizing user breaches of the terms. The process appears fair, but it could benefit from more explicit guidelines on how users can appeal or understand the reasons for termination, which would enhance user trust.
Termination and Account Suspension
8
Monica outlines the conditions under which accounts may be terminated or suspended, emphasizing user breaches of the terms. The process appears fair, but it could benefit from more explicit guidelines on how users can appeal or understand the reasons for termination, which would enhance user trust.
Monica Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8.2Data Collection:8.5
Data Usage:8
Data Sharing and Disclosure:7.5
User Rights and Controls:9
Data Security and Retention:8
Summary
Overall, Monica's Privacy Policy demonstrates a strong commitment to user privacy, with clear explanations of data collection, usage, and user rights. While the policy is generally well-structured and informative, there are areas for improvement, particularly in providing more detailed information about data sharing practices and simplifying complex language. The overall score reflects a solid foundation with room for enhancement.
Data Collection
8.5
Monica clearly outlines the types of data collected, including personal information like email addresses and technical data such as IP addresses and device IDs. The policy also mentions the use of cookies for tracking purposes. However, it could benefit from more detail on how data is collected from users and the specific types of content characteristics collected.
Data Collection
8.5
Monica clearly outlines the types of data collected, including personal information like email addresses and technical data such as IP addresses and device IDs. The policy also mentions the use of cookies for tracking purposes. However, it could benefit from more detail on how data is collected from users and the specific types of content characteristics collected.
Data Usage
8
The policy provides a comprehensive overview of how Monica uses personal data, including account management, service maintenance, and marketing communications. It also mentions targeted advertising and analytics. However, the explanation could be clearer regarding how user data is utilized for analytics and marketing purposes.
Data Usage
8
The policy provides a comprehensive overview of how Monica uses personal data, including account management, service maintenance, and marketing communications. It also mentions targeted advertising and analytics. However, the explanation could be clearer regarding how user data is utilized for analytics and marketing purposes.
Data Sharing and Disclosure
7.5
Monica specifies that it does not sell personal information and outlines the circumstances under which data may be shared with third parties, such as vendors and business partners. However, the policy could improve by providing more clarity on the types of third parties involved and the specific purposes for sharing data.
Data Sharing and Disclosure
7.5
Monica specifies that it does not sell personal information and outlines the circumstances under which data may be shared with third parties, such as vendors and business partners. However, the policy could improve by providing more clarity on the types of third parties involved and the specific purposes for sharing data.
User Rights and Controls
9
The policy effectively details user rights under GDPR and CCPA, including access, deletion, and opt-out options. It provides actionable steps for users to exercise these rights, which is commendable. However, it could enhance user understanding by simplifying the language used in some sections.
User Rights and Controls
9
The policy effectively details user rights under GDPR and CCPA, including access, deletion, and opt-out options. It provides actionable steps for users to exercise these rights, which is commendable. However, it could enhance user understanding by simplifying the language used in some sections.
Data Security and Retention
8
Monica describes the security measures in place to protect user data, including encryption and firewalls. The retention policy is also clearly stated, indicating that data will only be kept as long as necessary. More specific examples of security practices could further strengthen this section.
Data Security and Retention
8
Monica describes the security measures in place to protect user data, including encryption and firewalls. The retention policy is also clearly stated, indicating that data will only be kept as long as necessary. More specific examples of security practices could further strengthen this section.
Monica Rating
Not rated yet
0 ratings
Monica Comments
total: 0Monica AI Tool Family