neural.love
Unleash Your Creativity with Free AI Tools
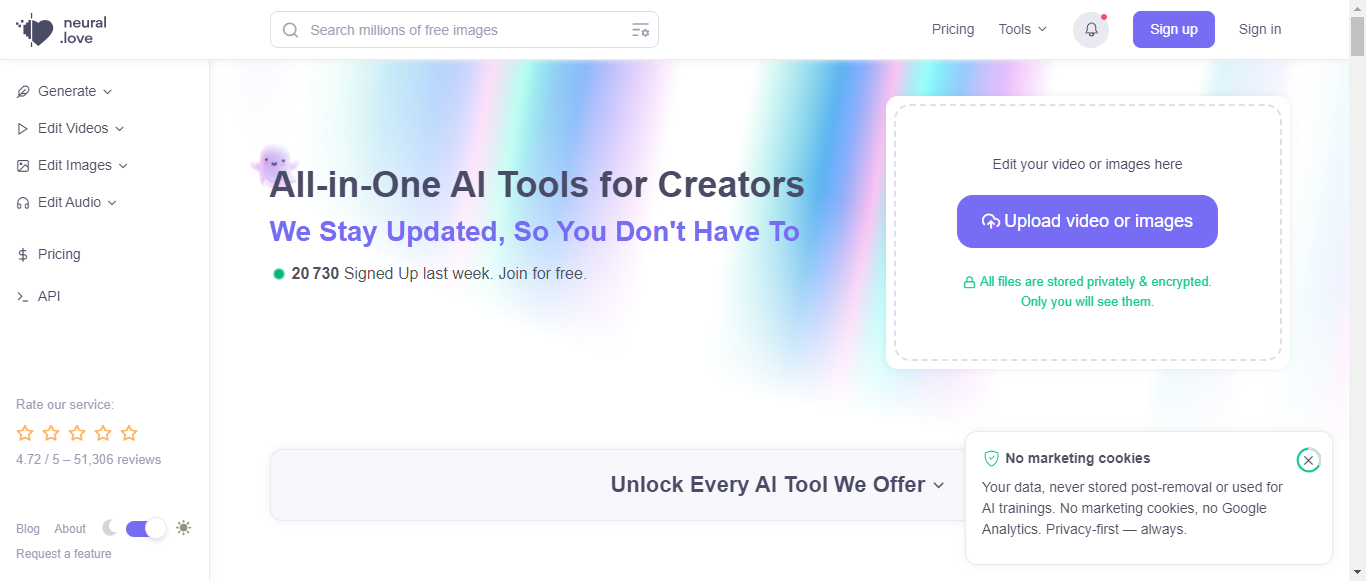

What is neural.love?
Neural.love offers a comprehensive suite of free AI tools designed for creators, enabling users to generate, enhance, and edit images, videos, and audio effortlessly. With a focus on privacy, the platform ensures that user data is never stored or used for AI training. The AI Image Generator allows users to create stunning visuals from simple text prompts, while the AI Photo Studio provides tailored images for various needs, such as CVs and social media profiles. Additionally, users can enhance the quality of their videos and audio files using advanced machine learning techniques. With over 60 million images generated and a commitment to continuous improvement, Neural.love is a go-to resource for anyone looking to leverage AI technology for creative projects. Join the growing community of creators and explore the endless possibilities of AI-driven content creation.
Categories
neural.love Pricing
Freemium
Starting from:
$0.17
- credit
neural.love ToS AI Analysis
Last Updated: February 10th, 2025 Tos Average Score: 8.2User Responsibilities and Restrictions:8.5
Intellectual Property Rights:9
Limitation of Liability and Disclaimers:8
Governing Law and Dispute Resolution:7.5
Termination and Account Suspension:8
Summary
Overall, the Terms of Service for Neural.love are well-structured and provide clear guidelines on user responsibilities, intellectual property rights, and limitations of liability. While the document is generally user-friendly, there are areas for improvement, particularly in simplifying legal language and enhancing clarity around dispute resolution and termination processes. The average score reflects a solid foundation with room for refinement.
User Responsibilities and Restrictions
8.5
Neural.love clearly outlines user responsibilities, including prohibited activities such as generating harmful content or violating laws. The section is comprehensive and emphasizes ethical use, which is commendable. However, it could benefit from more explicit examples of prohibited behaviors to enhance user understanding.
User Responsibilities and Restrictions
8.5
Neural.love clearly outlines user responsibilities, including prohibited activities such as generating harmful content or violating laws. The section is comprehensive and emphasizes ethical use, which is commendable. However, it could benefit from more explicit examples of prohibited behaviors to enhance user understanding.
Intellectual Property Rights
9
The Terms provide a clear framework regarding intellectual property, stating that users retain ownership of their content while granting Neural.love a non-exclusive license to use it. The distinction between user-generated content and AI-generated content is well-articulated, ensuring users understand their rights and the implications of using the service.
Intellectual Property Rights
9
The Terms provide a clear framework regarding intellectual property, stating that users retain ownership of their content while granting Neural.love a non-exclusive license to use it. The distinction between user-generated content and AI-generated content is well-articulated, ensuring users understand their rights and the implications of using the service.
Limitation of Liability and Disclaimers
8
Neural.love includes a robust disclaimer regarding the 'as is' nature of its services and limits liability for consequential losses. While this is standard practice, the language could be simplified for better user comprehension. Additionally, it might be beneficial to specify any exceptions to these limitations.
Limitation of Liability and Disclaimers
8
Neural.love includes a robust disclaimer regarding the 'as is' nature of its services and limits liability for consequential losses. While this is standard practice, the language could be simplified for better user comprehension. Additionally, it might be beneficial to specify any exceptions to these limitations.
Governing Law and Dispute Resolution
7.5
The Terms specify that they are governed by the laws of Estonia, which is clear. However, there is a lack of detailed procedures for dispute resolution, such as mediation or arbitration processes, which could provide users with more clarity on how disputes will be handled.
Governing Law and Dispute Resolution
7.5
The Terms specify that they are governed by the laws of Estonia, which is clear. However, there is a lack of detailed procedures for dispute resolution, such as mediation or arbitration processes, which could provide users with more clarity on how disputes will be handled.
Termination and Account Suspension
8
The conditions for account termination and suspension are outlined, allowing for immediate action in case of breaches. This is fair and transparent, but the process for users to appeal or understand the reasons for termination could be more explicitly stated to enhance user trust.
Termination and Account Suspension
8
The conditions for account termination and suspension are outlined, allowing for immediate action in case of breaches. This is fair and transparent, but the process for users to appeal or understand the reasons for termination could be more explicitly stated to enhance user trust.
neural.love Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8.6Data Collection:8.5
Data Usage:9
Data Sharing and Disclosure:8
User Rights and Controls:9
Data Security and Retention:8.5
Summary
Overall, the Privacy Policy for Neural.love is well-structured and provides clear information regarding data collection, usage, user rights, and security measures. The policy demonstrates a strong commitment to user privacy and compliance with GDPR. Areas for improvement include providing more specific examples in data sharing and enhancing details on data security protocols.
Data Collection
8.5
Neural.love provides a clear overview of the types of personal data collected, including information from customers, potential customers, partners, and job applicants. The methods of collection are well-defined, such as through account sign-ups, purchases, and communications. However, a more detailed explanation of the specific data points collected could enhance transparency.
Data Collection
8.5
Neural.love provides a clear overview of the types of personal data collected, including information from customers, potential customers, partners, and job applicants. The methods of collection are well-defined, such as through account sign-ups, purchases, and communications. However, a more detailed explanation of the specific data points collected could enhance transparency.
Data Usage
9
The policy effectively outlines the purposes for which personal data is used, including service delivery, customer relationship management, and compliance with legal obligations. It also mentions the use of Fathom Analytics for website performance without compromising user privacy, which is commendable. The clarity regarding the lawful bases for data processing is a strong point.
Data Usage
9
The policy effectively outlines the purposes for which personal data is used, including service delivery, customer relationship management, and compliance with legal obligations. It also mentions the use of Fathom Analytics for website performance without compromising user privacy, which is commendable. The clarity regarding the lawful bases for data processing is a strong point.
Data Sharing and Disclosure
8
Neural.love clearly states that personal data may be shared with data processors and professional advisors, ensuring that these parties adhere to data protection standards. However, the policy could benefit from more specific examples of third parties and circumstances under which data might be shared, particularly in relation to law enforcement.
Data Sharing and Disclosure
8
Neural.love clearly states that personal data may be shared with data processors and professional advisors, ensuring that these parties adhere to data protection standards. However, the policy could benefit from more specific examples of third parties and circumstances under which data might be shared, particularly in relation to law enforcement.
User Rights and Controls
9
The policy provides a comprehensive overview of user rights under GDPR, including access, rectification, erasure, and objection to processing. It also outlines actionable steps for users to exercise these rights, such as contacting the company directly. The commitment to respond within 30 days is a positive aspect.
User Rights and Controls
9
The policy provides a comprehensive overview of user rights under GDPR, including access, rectification, erasure, and objection to processing. It also outlines actionable steps for users to exercise these rights, such as contacting the company directly. The commitment to respond within 30 days is a positive aspect.
Data Security and Retention
8.5
Neural.love emphasizes its commitment to data security through various measures such as encryption and access control. The retention periods for different types of data are clearly stated, which is beneficial for user understanding. However, more detail on the specific security protocols in place could further strengthen this section.
Data Security and Retention
8.5
Neural.love emphasizes its commitment to data security through various measures such as encryption and access control. The retention periods for different types of data are clearly stated, which is beneficial for user understanding. However, more detail on the specific security protocols in place could further strengthen this section.
neural.love Rating
Not rated yet
0 ratings
neural.love Comments
total: 0neural.love AI Tool Family