Wonderway
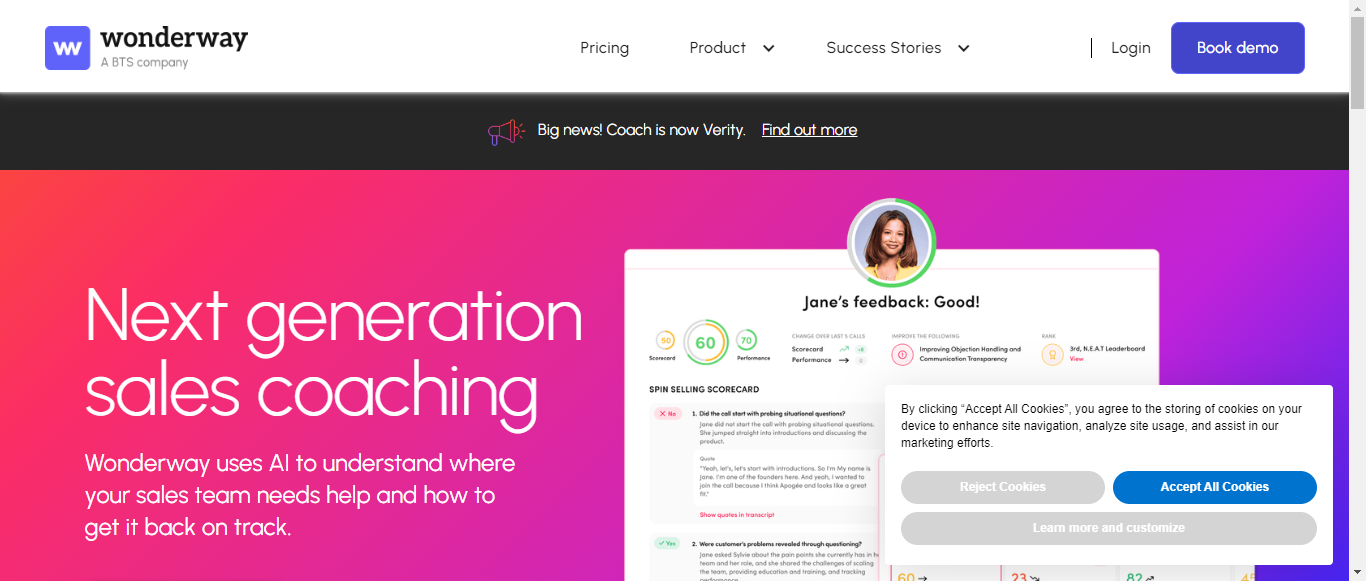
Transform Your Sales Team with AI-Powered Coaching on Every Call

What is Wonderway?
Wonderway is an innovative AI-driven sales training platform designed to enhance the performance of sales teams through automated coaching and personalized training. With its advanced machine learning capabilities, Wonderway analyzes sales calls to provide instant feedback, helping sales representatives identify their strengths and weaknesses. The platform boasts impressive success stories, including a 39% increase in conversion rates and a 50% reduction in ramp time for new hires. By automating sales coaching and quality assurance, Wonderway enables teams to improve at scale without the burden of sifting through countless call recordings. The platform also offers tailored training solutions for onboarding, upskilling, and certifications, ensuring that every team member receives the right guidance at the right time. With Wonderway, sales teams can expect to close more deals, align faster, and ultimately drive higher revenue.
Categories
Wonderway Pricing
Free Trial
Wonderway Privacy Policy AI Analysis
Last Updated: February 10th, 2025 Privacy Policy Average Score: 8.2Data Collection:8.5
Data Usage:8
Data Sharing and Disclosure:7.5
User Rights and Controls:9
Data Security and Retention:8
Summary
Overall, Wonderway's Privacy Policy is well-structured and informative, providing a solid understanding of data collection, usage, sharing, user rights, and security measures. Key strengths include a clear explanation of user rights and comprehensive data collection practices. Areas for improvement include enhancing transparency in data sharing and providing more specific examples in the data usage and security sections.
Data Collection
8.5
Wonderway provides a comprehensive overview of the types of data collected, including personal information from clients, vendors, and users of their services. The policy clearly outlines the methods of collection, such as through account creation, Google APIs, and cookies. However, it could benefit from a more concise summary of the data types to enhance clarity.
Data Collection
8.5
Wonderway provides a comprehensive overview of the types of data collected, including personal information from clients, vendors, and users of their services. The policy clearly outlines the methods of collection, such as through account creation, Google APIs, and cookies. However, it could benefit from a more concise summary of the data types to enhance clarity.
Data Usage
8
The policy effectively details the purposes for which data is used, including service improvement, marketing, and legal compliance. It emphasizes the legitimate interests of Wonderway in processing data. However, the section could be improved by providing more specific examples of how data is used for analytics and marketing.
Data Usage
8
The policy effectively details the purposes for which data is used, including service improvement, marketing, and legal compliance. It emphasizes the legitimate interests of Wonderway in processing data. However, the section could be improved by providing more specific examples of how data is used for analytics and marketing.
Data Sharing and Disclosure
7.5
Wonderway outlines the circumstances under which data may be shared, including with affiliates, service providers, and in legal situations. While the policy is generally clear, it could enhance transparency by specifying the types of third parties involved and the nature of the data shared.
Data Sharing and Disclosure
7.5
Wonderway outlines the circumstances under which data may be shared, including with affiliates, service providers, and in legal situations. While the policy is generally clear, it could enhance transparency by specifying the types of third parties involved and the nature of the data shared.
User Rights and Controls
9
The policy does an excellent job of explaining user rights under GDPR, including access, deletion, and the right to object. It provides actionable steps for users to exercise these rights, which is commendable. However, it could include more information on how users can easily contact Wonderway for assistance.
User Rights and Controls
9
The policy does an excellent job of explaining user rights under GDPR, including access, deletion, and the right to object. It provides actionable steps for users to exercise these rights, which is commendable. However, it could include more information on how users can easily contact Wonderway for assistance.
Data Security and Retention
8
Wonderway describes various security measures in place to protect personal information and outlines the retention policy based on legal requirements and business needs. While the information is generally clear, it could benefit from more specific details on the security technologies used.
Data Security and Retention
8
Wonderway describes various security measures in place to protect personal information and outlines the retention policy based on legal requirements and business needs. While the information is generally clear, it could benefit from more specific details on the security technologies used.
Wonderway Rating
Not rated yet
0 ratings
Wonderway Comments
total: 0Wonderway AI Tool Family